Best Data Privacy Software RFP Template and Response Guide
How prepared is your team to respond when a high-stakes data privacy software RFP lands in your inbox? As buyers are asking tougher questions about compliance, security, and data governance than ever before.
If you're part of a sales or proposal team, you know what follows: lengthy security questionnaires, detailed compliance matrices, and multiple SMEs chasing deadlines. One missed requirement or outdated response can cost you the deal.
In this blog, we'll explore a ready-to-use data privacy software RFP template, a detailed vendor response template, and practical tips to customize your answers so you can submit stronger, more compliant proposals with confidence.
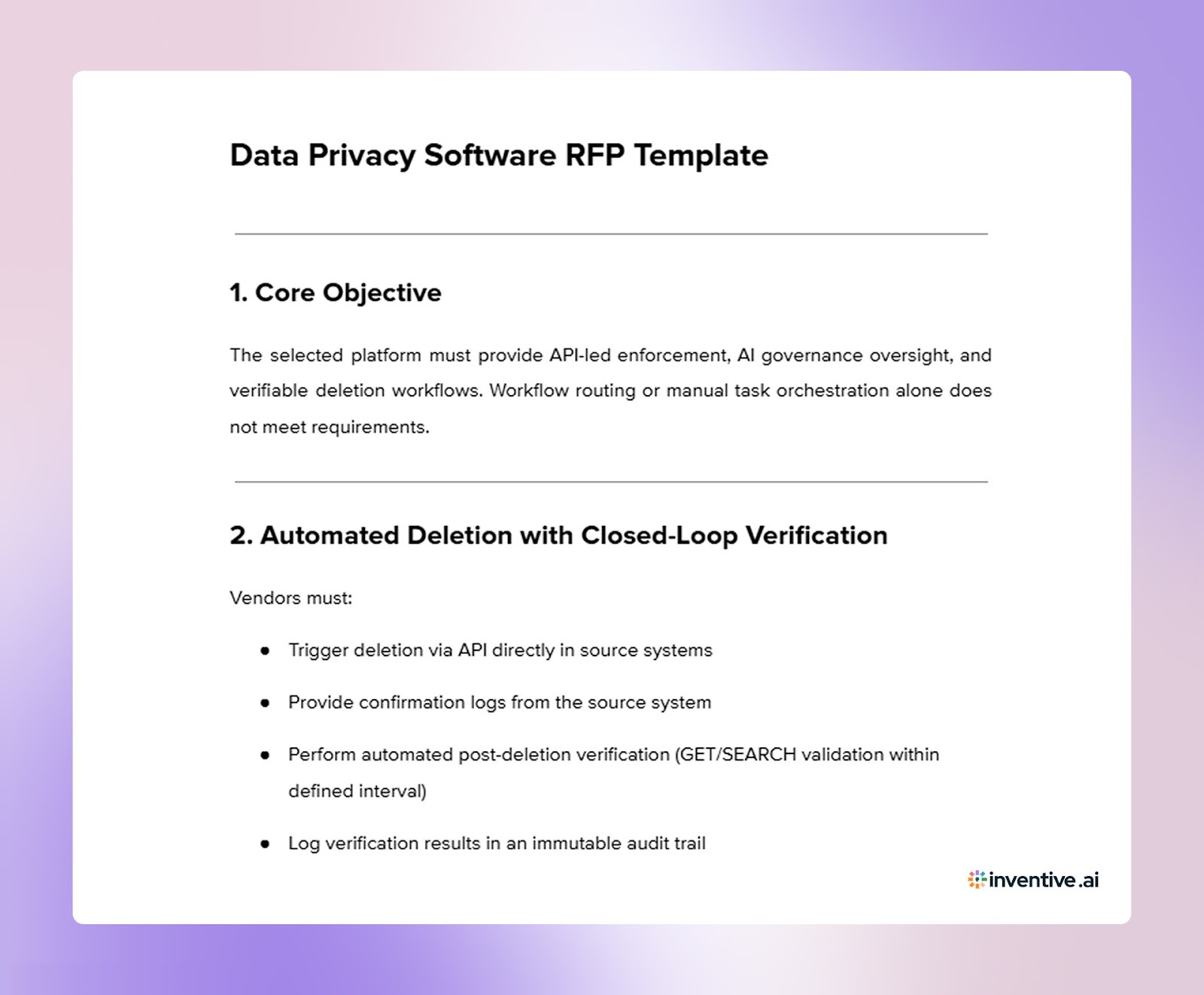
Data Privacy Software RFP Template for 2026 (for Buyers)
Organizations are no longer evaluating privacy software only for regulatory coverage. They are evaluating it for AI accountability, automated enforcement, and executive-level visibility.
Below is a comprehensive data privacy software RFP template you can use as a reference when issuing a data privacy software RFP.

Now that you understand what buyers include in a data privacy software RFP, you can structure a response that directly addresses those expectations.
Data Privacy Software RFP Response Template for Vendors
Use this structured template to respond to modern data privacy software RFPs focused on AI governance, API-led enforcement, and verifiable compliance. Replace bracketed placeholders with your company's details.
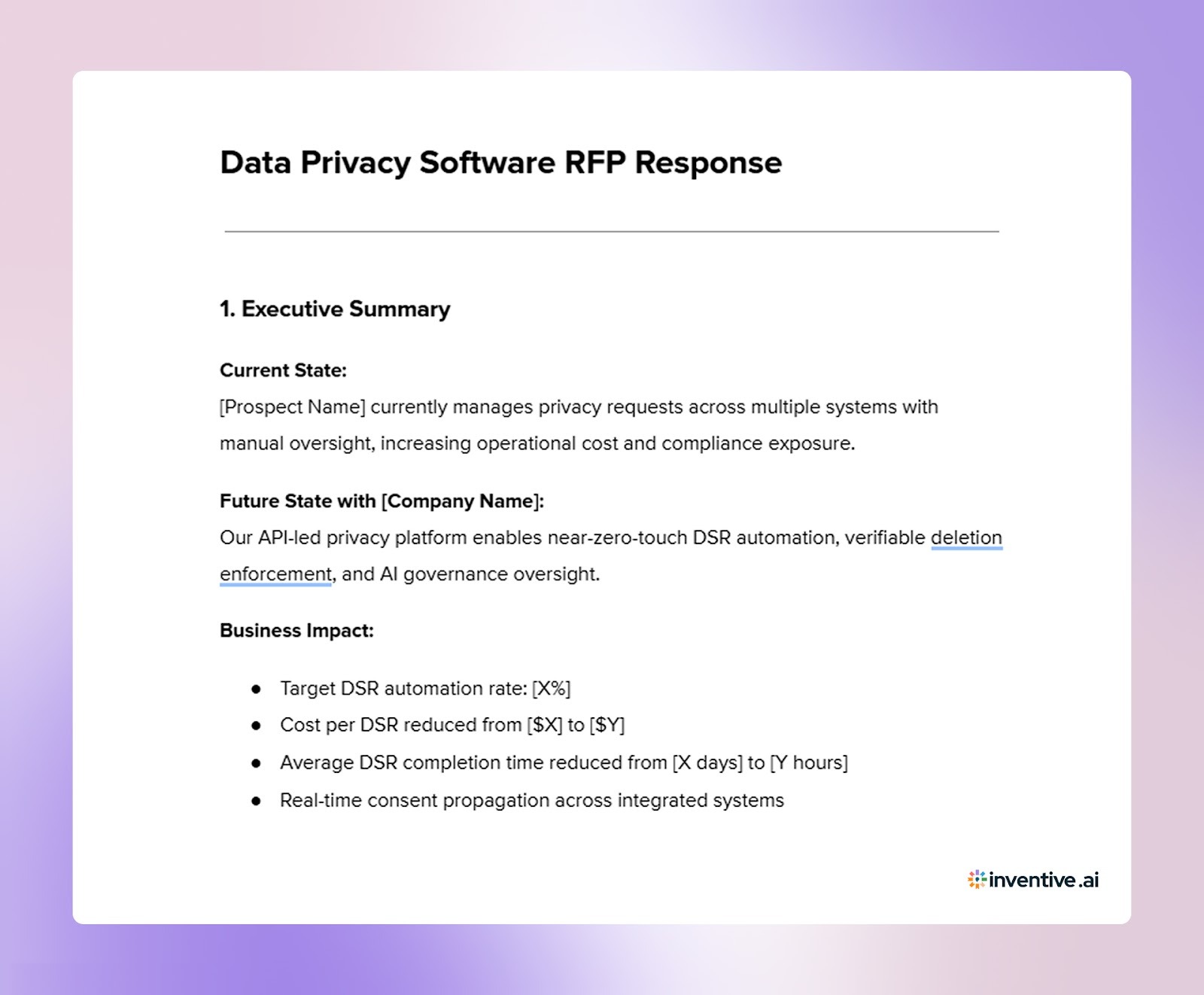

1. Executive Summary
Current State:
[Prospect Name] currently manages privacy requests across multiple systems with manual oversight, increasing operational cost and compliance exposure.
Future State with [Company Name]:
Our API-based privacy platform delivers near-zero-touch DSR automation, verifiable deletion control, and oversight for AI governance.
Business Impact:
- Target DSR automation rate: [X%]
- Cost per DSR reduced from [$X] to [$Y]
- Average DSR completion time reduced from [X days] to [Y hours]
- Real-time consent propagation across integrated systems
Estimated time to value: [X weeks]
2. Company Overview & Vendor Viability
- Year Founded: [Year]
- Headquarters: [Location]
- Total Customers: [Number]
- Customer Retention Rate: [Metric]
- Annual Churn Rate: [Metric]
- Roadmap drivers: [% Regulatory] / [% Customer-driven]
3. Technical Architecture & Automation Integrity
Deletion & Verification Flow
Automation-to-Manual Ratio
Resiliency & Rate Limiting
- API retry logic: Yes / No
- Backoff strategy: [Description]
- Failure alerts triggered: Yes / No
4. Data Discovery & Classification Controls
Coverage
- Structured Systems: [Databases / Warehouses]
- Unstructured Systems: [Slack, Email, Drives]
- OCR for scanned documents: Yes / No
Accuracy & Safeguards
- F1 Score: [Metric]
- Precision: [Metric]
- Recall: [Metric]
- Human-in-the-loop review before destructive deletion: Yes / No
- Classification override audit trail: Yes / No
Describe how false positives are mitigated operationally.
5. AI Governance & Shadow AI Controls
AI System Inventory
Describe the automated cataloging process for AI/ML systems.
Shadow AI Detection
- Browser extension monitoring required: Yes / No
- Network-level monitoring: Yes / No
- Endpoint agent required: Yes / No
Right to Be Forgotten (AI Context)
Explain:
- Retraining approach
- Suppression layers
- Known technical limitations
6. Consent Capture, Propagation & Performance
7. Regulatory & Centralized Portal Handling
Supported frameworks:
- GDPR
- CCPA / CPRA
- California DELETE Act (SB 362)
- India DPDPA
- CPPA centralized portal ingestion: Yes / No
- DPDPA Consent Manager interoperability: Yes / No
8. Data Residency & Vendor Processing Transparency
- Primary processing regions: [Regions]
- Metadata storage location: [Location]
- Cross-border safeguards: [Description]
- Regional failover controls: [Details]
9. Security & Vulnerability Management
- Encryption standards: [Details]
- Penetration testing frequency: [Quarterly / Annual]
- Bug bounty program: Yes / No
- Incident response SLA: [Metric]
- Insurance coverage: [Details]
10. Data Minimization & Retention Enforcement
- ROT detection capability: Yes / No
- Automated retention enforcement: Yes / No
- Direct deletion at source systems: Yes / No
Authorization & Logging
- Role-based deletion authorization: Yes / No
- Immutable verification logs: Yes / No
- Audit export capability: Yes / No
11. Implementation Plan & Customer Effort
Success Criteria
- Automation rate target: [Metric]
- Response time reduction target: [Metric]
- Audit readiness milestone: [Description]
12. Training & Change Management
- Admin UI training provided: Yes / No
- Legal/HR workflow training: Yes / No
- Documentation library access: Yes / No
- Dedicated Customer Success Manager: Yes / No
13. Vendor Risk & Sub-Processor Governance
- Sub-processor monitoring: Yes / No
- Automated DTIA generation: Yes / No
- Privacy notice update automation: Yes / No
14. Developer Experience
- SDK documentation access: Yes / No
- Sandbox environment: Yes / No
- CI/CD integration support: Yes / No
- Estimated engineering hours required: [Metric]
15. Architectural Differentiators
Unlike legacy privacy platforms that rely on centralized data crawling and replication, our architecture:
- Uses API-led pointer-based deletion
- Avoids unnecessary PII ingestion
- Reduces data gravity risks
- Supports direct source-system enforcement
- Maintains regional data control
16. Compliance Matrix Summary
While a structured template gives you a strong starting point, customizing your response is what ultimately improves evaluation scores.
How to Customize Your Data Privacy Software RFP Response?
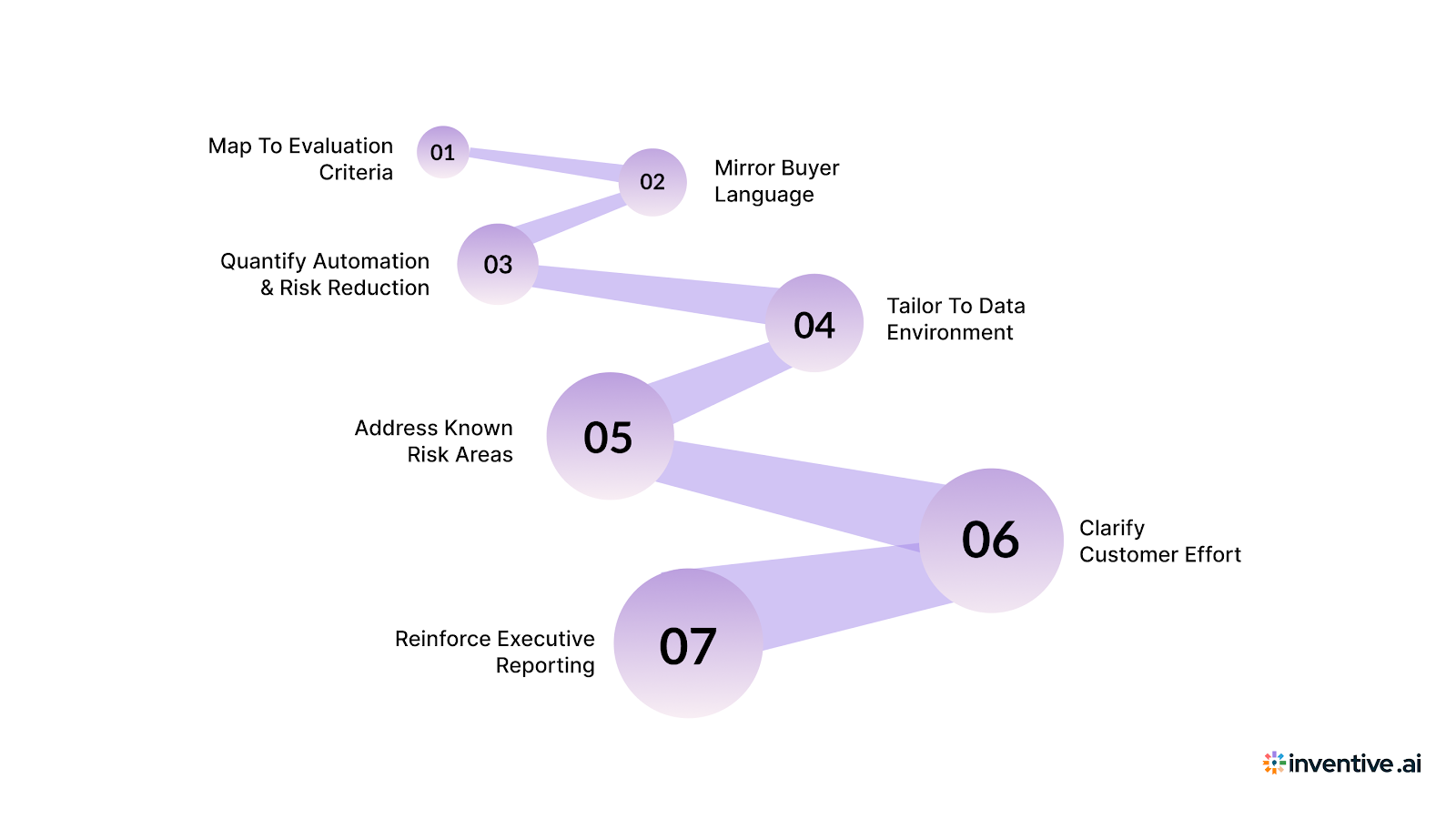
A strong template gives you structure, but winning responses are customized to the buyer's regulatory exposure, data footprint, and risk tolerance. Generic answers signal low effort and increase the chance of follow-up questions. Your goal is to connect each requirement to the prospect's specific environment, priorities, and scoring model.
Before finalizing your submission, refine your response using the steps below:
- Map to the Evaluation Criteria: Review the buyer's weighted scoring model and adjust depth accordingly. If AI governance carries 25%, expand your model oversight and deletion verification sections with metrics and proof.
- Mirror the Buyer's Language: Reuse the exact regulatory terms and requirement labels from the RFP. If they reference the California DELETE Act or DPDPA Consent Managers, address those explicitly rather than replying with generic "US state law support."
- Quantify Automation & Risk Reduction: Replace feature descriptions with measurable outcomes: automation ratio, DSR turnaround time, consent sync SLA, and audit log retention periods.
- Customize by Data Environment: Specify integrations that match their stack (e.g., Salesforce, Snowflake, Slack). Mention deletion verification flows relevant to their systems, not a generic architecture diagram.
- Address Known Risk Areas Upfront: If your classification accuracy is 95%, explain how the remaining margin is handled with human review buffers and override logging.
- Clarify Customer Effort: Outline the client resources required during onboarding. Transparency about time and staffing builds trust and reduces procurement friction.
- Reinforce Executive Reporting: Highlight board-ready dashboards, risk scoring summaries, and compliance export capabilities if the RFP emphasizes oversight.
To sustain high-quality responses at scale, you need AI-powered automation that understands context rather than recycling generic answers.
Why Proposal Teams Use Inventive AI for Data Privacy RFP Responses?
Responding to modern privacy RFPs requires more than pulling answers from a content library. You need context awareness, consistency across sections, and proof that your responses meet compliance and AI governance expectations. That is where Inventive AI supports proposal, sales, and security teams working under tight deadlines.
Here is how Inventive AI helps you submit stronger, more defensible responses:
Context Engine:
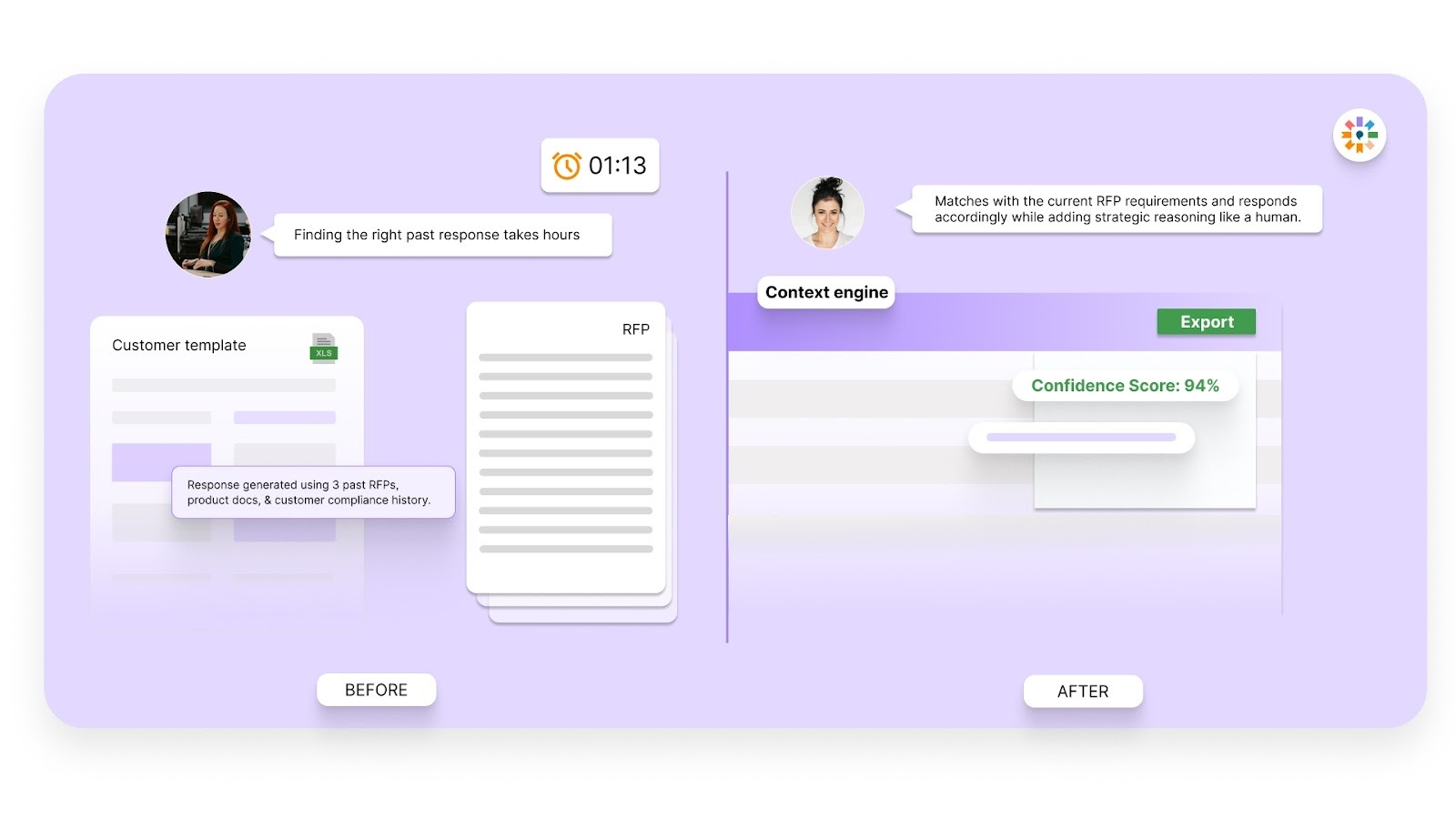
Unlike basic chat-based tools that generate generic answers, Inventive AI's multi-layer reasoning engine reads the entire RFP before drafting responses. It understands dependencies between sections, so your AI governance answer aligns with your deletion workflow, consent model, and security posture.
Conflict Detection:
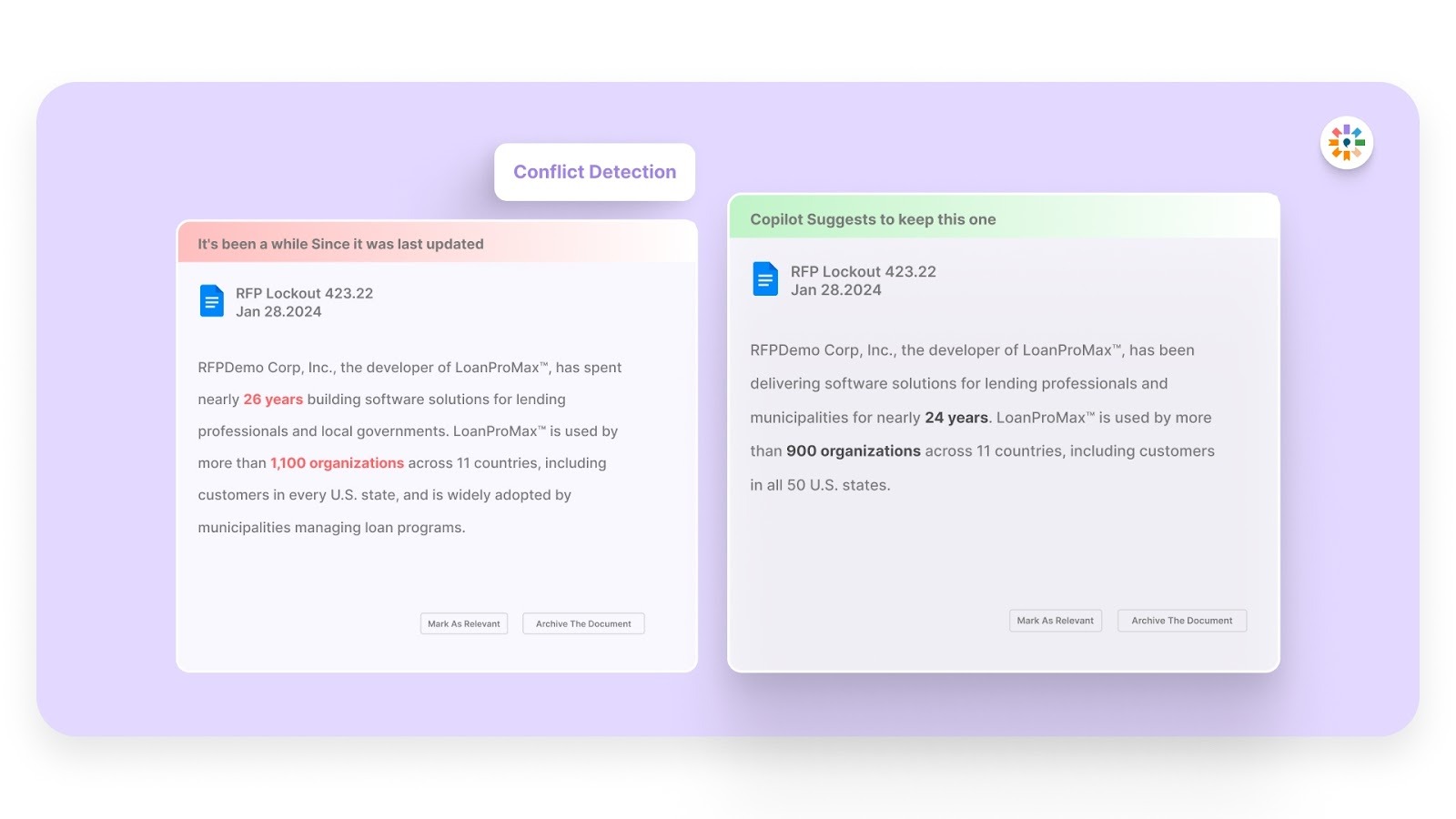
Inventive AI automatically flags inconsistent claims across your response. If one section states fully automated deletion and another implies manual approval, the system highlights the mismatch before submission, reducing compliance and credibility risks.
Outdated Content Detection:
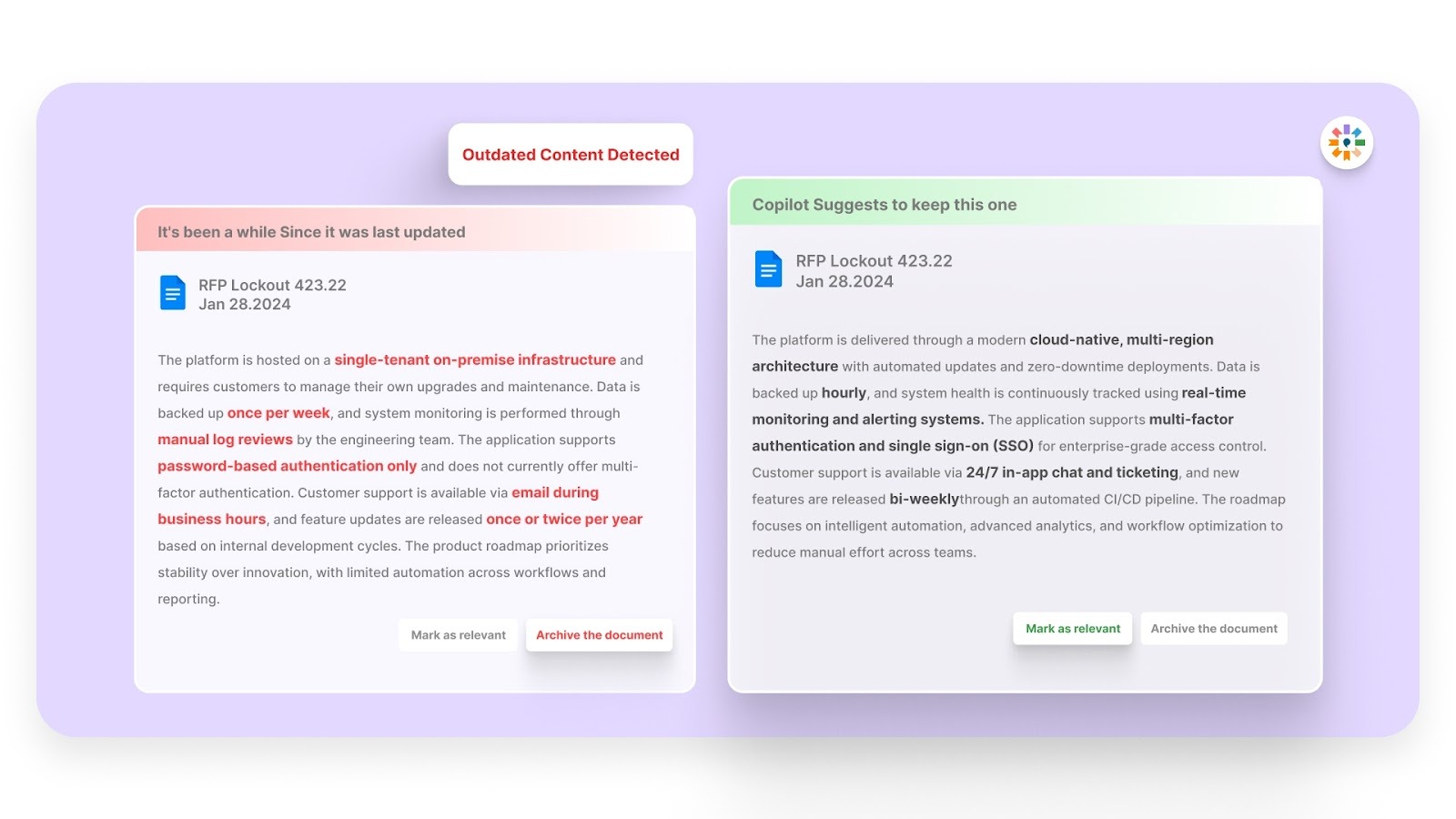
Large answer libraries often contain expired certifications or legacy regulatory references. Inventive AI scans your knowledge sources and surfaces outdated or non-compliant content, helping teams avoid sending incorrect information.
2X Higher-Quality Responses:
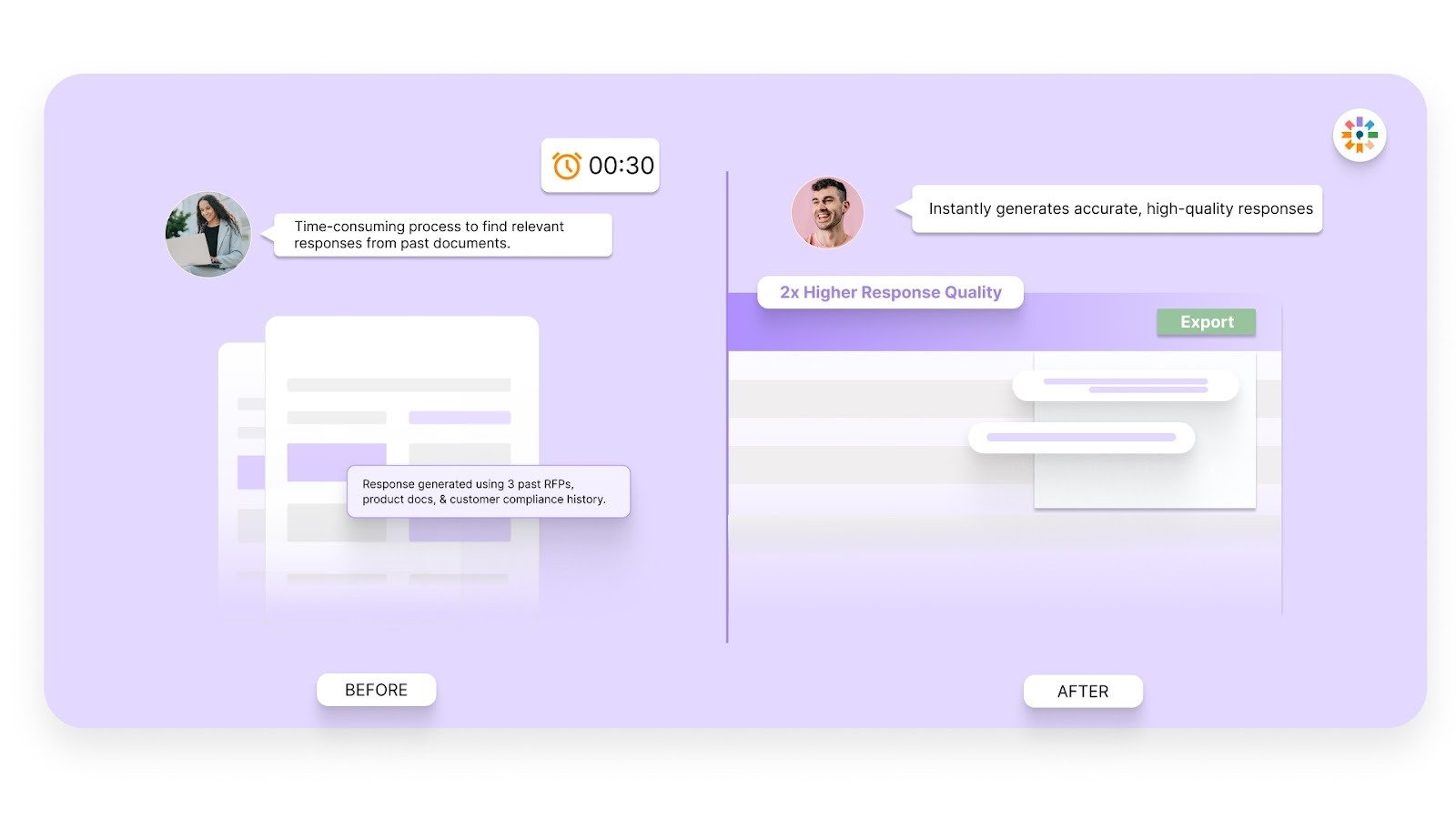
Inventive AI uses specialized AI agents to interpret intent, structure strategic answers, and improve clarity and completeness. The result is responses that read like they were written by a subject matter expert, not assembled from disconnected fragments.
Simple and Easy-to-Use Interface:
With a 100 percent adoption rate among its existing customers and a ranking as the number one easiest-to-use RFP software on G2, Inventive AI helps proposal, sales, and security teams get started quickly, even without previous experience with AI tools.
When privacy RFPs demand accuracy, consistency, and proof rather than promises, Inventive AI helps your team respond with confidence.
FAQs
1. How long should a data privacy software RFP response be?
Length should reflect the complexity of the buyer's requirements rather than a fixed page count. Enterprise privacy RFP responses often range from 25 to 80 pages, depending on regulatory scope and technical depth. Focus on completeness and clarity instead of adding unnecessary narrative.
2. Who should be involved in preparing a privacy RFP response?
A strong response typically requires input from security, legal, engineering, and product teams. Proposal managers coordinate timelines and messaging, while subject matter experts validate technical and compliance details before submission.
3. How can you reduce back-and-forth questions after submission?
Anticipate clarification requests by addressing assumptions directly in your response. Define technical terms, explain architectural limitations, and provide supporting metrics so evaluators do not need to request additional detail.
4. What documents should you attach to a privacy RFP response?
Common attachments include security certifications, penetration test summaries, data processing agreements, sub-processor lists, and architectural diagrams. Including these proactively signals preparedness and reduces procurement delays.
5. How do you prepare for a privacy-focused vendor demo after submitting your response?
Align your demo agenda with the highest-weighted evaluation criteria in the RFP. Be ready to walk through deletion workflows, reporting dashboards, and governance controls in a structured, time-bound format that matches your written claims.

90% Faster RFPs. 50% More Wins. Watch a 2-Minute Demo.
After witnessing the gap between generic AI models and the high precision required for business proposals, Gaurav co-founded Inventive AI to bring true intelligence to the RFP process. An IIT Roorkee graduate with deep expertise in building Large Language Models (LLMs), he focuses on ensuring product teams spend less time on repetitive technical questionnaires and more time on innovation.

