Cyber Security DDQ Template: A Vendor’s Guide (2026)
.jpg)
Responding to Due Diligence Questionnaires (DDQs) in cybersecurity is no small task. In industries where security is a top priority, the questions you answer must demonstrate your company’s ability to manage risk, protect data, and comply with regulations. But how do you ensure that your responses stand out and are both thorough and accurate?
This is where an effective DDQ template comes into play. By utilizing a well-organized template, you can simplify your response process, maintain consistency, and ensure accuracy without sacrificing quality.
In this blog, let's understand the importance of DDQs in cybersecurity, how to respond effectively, and how AI-powered tools can help simplify this process for you.
Key Takeaways
- DDQs Assess Cybersecurity Practices: DDQs focus on evaluating how vendors manage security risks, protect data, and comply with industry regulations like HIPAA, GDPR, and FISMA.
- Industry-Specific Requirements: Different sectors (finance, healthcare, government) have unique cybersecurity requirements that vendors need to address in their DDQ responses.
- DDQ Components: Key sections in cybersecurity DDQs include security posture, data encryption, access control, incident response, compliance, and third-party risk management.
- Best Practices for Responding: Be clear and concise, use evidence, tailor responses to buyer needs, and maintain consistency across your answers to improve your chances of success.
- Inventive AI DDQ Responses Software Helps Improve Efficiency: Inventive AI automates the drafting process, ensuring high-quality, consistent, and up-to-date responses while saving time and reducing errors.
Comprehensive Cyber Security DDQ Template for Effective Risk Management
About the Cyber Security DDQ Template
This Cyber Security DDQ template is an easy-to-use tool that helps vendors provide clear and accurate responses to cybersecurity due diligence questionnaires. Designed for industries like finance, healthcare, and government, this template covers all key areas to show your firm’s security practices, risk management, and compliance with regulations.
What This Template Includes:
- Security Posture: Sections to explain your company’s overall security strategy and threat management.
- Data Protection and Encryption: Guidelines for detailing how you protect data, both in storage and during transmission.
- Access Control: Space to describe your user authentication methods and access controls like multi-factor authentication.
- Incident Response: Areas to explain your response plan for security incidents, including how you manage and report breaches.
- Compliance and Certifications: A section to list your relevant certifications, such as SOC 2 or ISO 27001, showing your adherence to industry standards.
- Third-Party Risk Management: Sections to describe how you evaluate and manage security risks from third-party vendors.
Why Use This Template?
- Consistency: This template keeps your responses consistent, making it easier for buyers to evaluate your company.
- Saves Time: You can quickly create detailed responses using a pre-designed structure, saving valuable time.
- Comprehensive Coverage: The template ensures you cover all the areas that buyers care about when assessing cybersecurity practices.
- Easy Collaboration: The template makes it simple for different teams (security, compliance, legal) to work together on the DDQ responses.
Using this Cyber Security DDQ template helps you provide clear, thorough responses, boosting your chances of winning contracts and showing buyers that your company is committed to security and compliance.

Tips for Customizing the Cyber Security DDQ Template
Customizing the Cyber Security DDQ template helps you provide accurate and tailored responses that highlight your company's security practices. Here are some simple tips to make sure your responses stand out:
1. Align with Your Security Policies: Ensure the template reflects your company’s actual security practices. Tailor sections like your security posture and risk management to match your internal policies.
2. Provide Specific Encryption Details: Be clear about the encryption methods you use, such as AES-256 or TLS, to protect sensitive data both at rest and in transit. This shows compliance with industry standards.
3. Update Compliance Information: Regularly update the template with the latest certifications, such as ISO 27001 or GDPR, to demonstrate your compliance with current regulations.
4. Attach Supporting Documents: Whenever possible, include proof of your security measures, such as audit reports or certifications, to support your answers.
5. Customize Access Control Details: Detail how you manage access to sensitive information, mentioning tools like multi-factor authentication (MFA) or Single Sign-On (SSO) that your company uses.
6. Explain Your Incident Response Process: Clearly describe your steps for handling security incidents, including how you communicate with stakeholders and the timeline for resolution.
7. Clarify Third-Party Risk Management: Mention how you assess the security of third-party vendors, ensuring they meet your security standards through regular audits or assessments.
By customizing the DDQ template in these ways, you ensure that your responses are specific, relevant, and aligned with your company's actual security practices.
Also Read: How to Develop Effective RFP Win Themes for Proposal Success
The Six Core Sections of Cyber Security DDQs Template for Trust and Reliability
Cybersecurity DDQs are used by buyers to assess how well your company manages cybersecurity risks. These questionnaires typically cover several key areas:
1. General Security Posture
This section asks about your company’s overall security policies and procedures. You’ll need to explain your security frameworks, how you monitor for threats, and how your team manages security risks.
2. Data Protection and Encryption
Here, you’ll be asked about how you protect sensitive data. Expect questions about data encryption, how your company keeps data safe when it’s stored (at rest) and during transmission (in transit). You'll likely need to explain which encryption standards you use and how you manage encryption keys.
3. Access Control
This section focuses on how you control who can access sensitive data and systems. You’ll answer questions about multi-factor authentication (MFA), role-based access controls, and how you make sure only authorized users can access critical data.
4. Incident Response and Reporting
Buyers will want to know how you respond to security incidents. This section covers your incident response plan, how quickly you detect and respond to breaches, and how you report them according to regulatory requirements like GDPR.
5. Compliance and Certifications
You’ll be asked to provide information about any industry certifications your company holds, such as ISO 27001, SOC 2, or PCI DSS. Buyers want to know that you comply with industry standards and regulations related to cybersecurity.
6. Third-Party Risk Management
This section looks at how you manage risks from third-party vendors. You’ll be asked about how you assess and monitor the security of vendors, especially those that have access to sensitive data or systems.
Understanding the main components of a cybersecurity DDQ helps you prepare clear, complete responses that show you’re ready to meet buyers' security needs. By addressing areas like your security posture, data protection practices, and incident response plan, you’ll be able to demonstrate your company’s cybersecurity expertise.
6 Steps to Structuring Strong Cybersecurity DDQ Responses
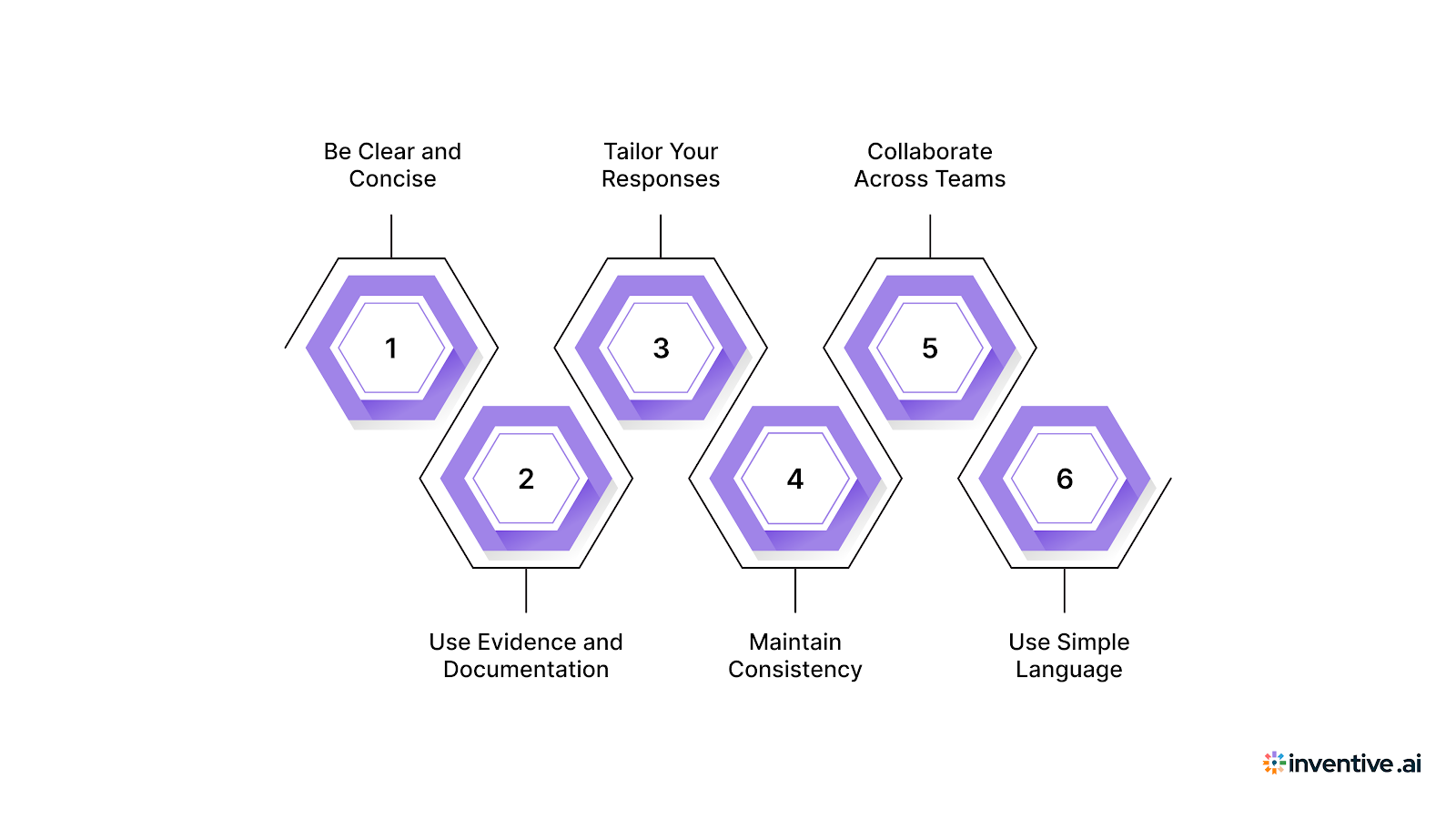
Responding to cybersecurity DDQs can be challenging, especially when dealing with multiple detailed questions that often require input from different teams.
Here are some best practices to help you respond effectively and efficiently:
1. Be Clear and Concise
Avoid lengthy, jargon-heavy explanations. Provide straightforward answers that directly address the buyer's questions. This helps prevent confusion and keeps the focus on your company’s security strengths. Stay concise while ensuring you answer everything the buyer needs to know.
2. Use Evidence and Documentation
Support your answers with evidence whenever possible. This could include certifications (like ISO 27001, SOC 2, or PCI DSS), recent audit reports, or real-life examples of your security protocols in action. Providing proof not only strengthens your credibility but also gives the buyer confidence in your capabilities.
3. Tailor Your Responses
Customize your answers to fit the specific needs and concerns of the buyer. For example, if you're responding to a healthcare provider, focus on HIPAA compliance, explain how you manage patient data privacy, and outline your data protection strategies. Tailoring your responses shows that you’ve carefully reviewed the buyer’s concerns and are prepared to meet their unique requirements.
4. Maintain Consistency
Ensure that your responses are consistent with your company’s security policies and strategies. Double-check that all answers align with your internal practices. Avoid contradictions or outdated information that could raise doubts. Consistency is key to portraying your organization as reliable and trustworthy.
5. Collaborate Across Teams
To ensure accuracy, involve all relevant teams in the process. Your legal, technical, and compliance teams should review the DDQ responses to verify that the information is correct and up-to-date. This collaborative approach ensures that responses are comprehensive and legally compliant.
6. Use Simple Language
Cybersecurity can be a complex topic, but when responding to DDQs, it’s important to simplify technical language. Avoid overwhelming the buyer with overly technical terms unless necessary, and focus on clear, understandable explanations that can be easily followed by non-technical stakeholders.
By following these best practices, you’ll be able to respond to cybersecurity DDQs effectively, with high-quality, accurate, and relevant answers. This not only saves time but also shows your organization’s commitment to cybersecurity practices.
4 Industries Where Cyber-Security DDQs Are Common
DDQs aren’t uniform across all industries. Each sector has its own set of security priorities and regulations, which shape the content and focus of cybersecurity DDQs.
Here's how these industry-specific DDQs influence how vendors should respond:
1. Finance
In the financial sector, DDQs focus on protecting sensitive financial data and ensuring compliance with regulations like the Gramm-Leach-Bliley Act (GLBA) and Sarbanes-Oxley Act (SOX). You’ll be asked about data encryption practices, fraud prevention, access controls, and disaster recovery plans. Financial buyers want to know how you secure transactions and protect sensitive financial information.
2. Healthcare
Healthcare DDQs focus on HIPAA compliance, ensuring that vendors protect patient data. Expect questions about your data encryption methods, access controls, incident response plans, and data retention practices. Healthcare providers will also want to know how you ensure audit trails and handle breach notifications.
3. Government
Government contracts require compliance with regulations like FISMA and NIST SP 800-53. DDQs will ask about your company’s risk management frameworks, incident response protocols, and system security certifications. You'll also need to demonstrate how you protect sensitive government data and manage supply chain security.
4. Tech Companies
For tech vendors, DDQs focus on software vulnerabilities, patch management, and third-party risk management. Expect questions about how you secure your software, implement regular patching, and manage risks from external partners. Tech buyers will also want to know about your cloud security and how you maintain a secure development process.
Each industry has unique cybersecurity requirements, and tailoring your responses to these specific needs is key to improving your chances of winning the contract.
3 Real-World Cybersecurity DDQ Examples by Industry
Understanding how DDQs are used in real-world situations can help you create better, more tailored responses.
Here are three realistic examples from industries with strict cybersecurity requirements:
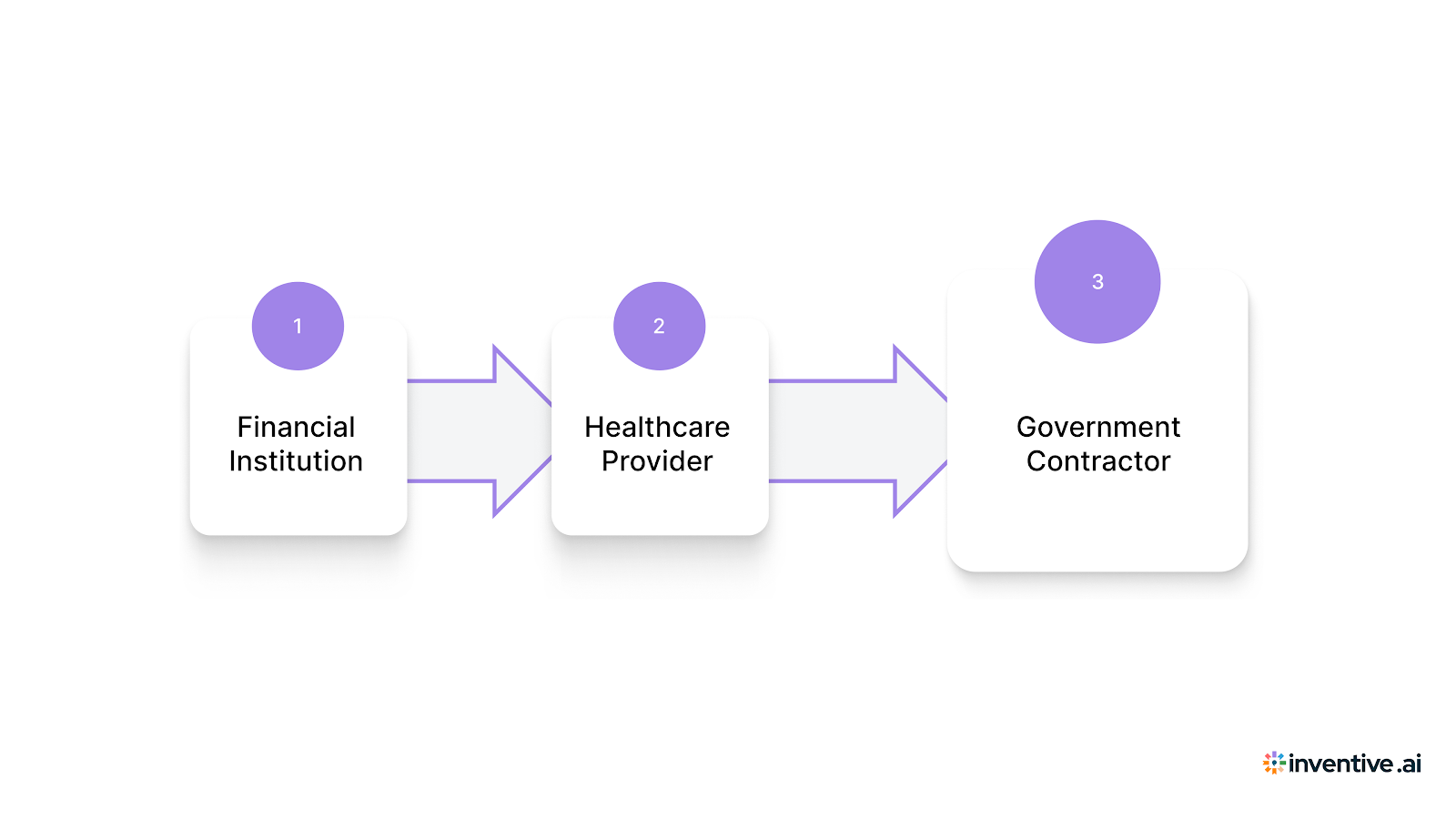
1. Financial Institution
Scenario: A global financial services provider issues a DDQ to assess the security practices of a technology vendor seeking to handle sensitive financial data.
The DDQ will likely focus on questions about data encryption standards (e.g., AES-256 for data at rest), multi-factor authentication (MFA) for system access, and fraud prevention measures. It may also ask for your company’s disaster recovery plan, ensuring that you can maintain access to financial systems in the event of a cyber attack.
Additionally, the DDQ could inquire about third-party risk management practices to ensure that no external vendors pose a security threat.
2. Healthcare Provider
Scenario: A healthcare provider requires a vendor to demonstrate HIPAA compliance before entering into a business agreement.
The DDQ will include questions about how your company handles patient data protection (e.g., encryption of electronic health records), the access controls in place to limit who can view patient data, and the incident response procedures to follow in case of a data breach.
The questionnaire may also ask how your organization handles data retention and ensures that outdated patient data is securely deleted in compliance with HIPAA regulations.
3. Government Contractor
Scenario: A U.S. government agency issues a DDQ to evaluate a vendor's ability to protect federal data in compliance with FISMA (Federal Information Security Modernization Act).
The DDQ will focus on security framework adherence, asking whether the vendor follows NIST SP 800-53 guidelines for security controls.
Additionally, it will ask about the vendor’s ability to maintain data integrity and availability, including backups, disaster recovery protocols, and incident reporting procedures. Questions may also address how the vendor complies with CMMC (Cybersecurity Maturity Model Certification), which is required for Department of Defense contractors.
By examining these real-world DDQ examples, you can gain a better understanding of the types of questions you might encounter and how to structure your responses effectively.
Also Read: Top 25 RFP Software in 2025: Which to Use?
Simplify Your Cybersecurity DDQ Responses with Inventive AI
Responding to cybersecurity DDQs is an important but time-consuming task, often requiring input from multiple teams and careful attention to detail. With Inventive AI’s AI-powered RFP automation, you can cut down on the time spent drafting responses and increase the accuracy and quality of your submissions, making your team more efficient.
Why Inventive AI is the Best:
1. 2x More Accurate Response Quality
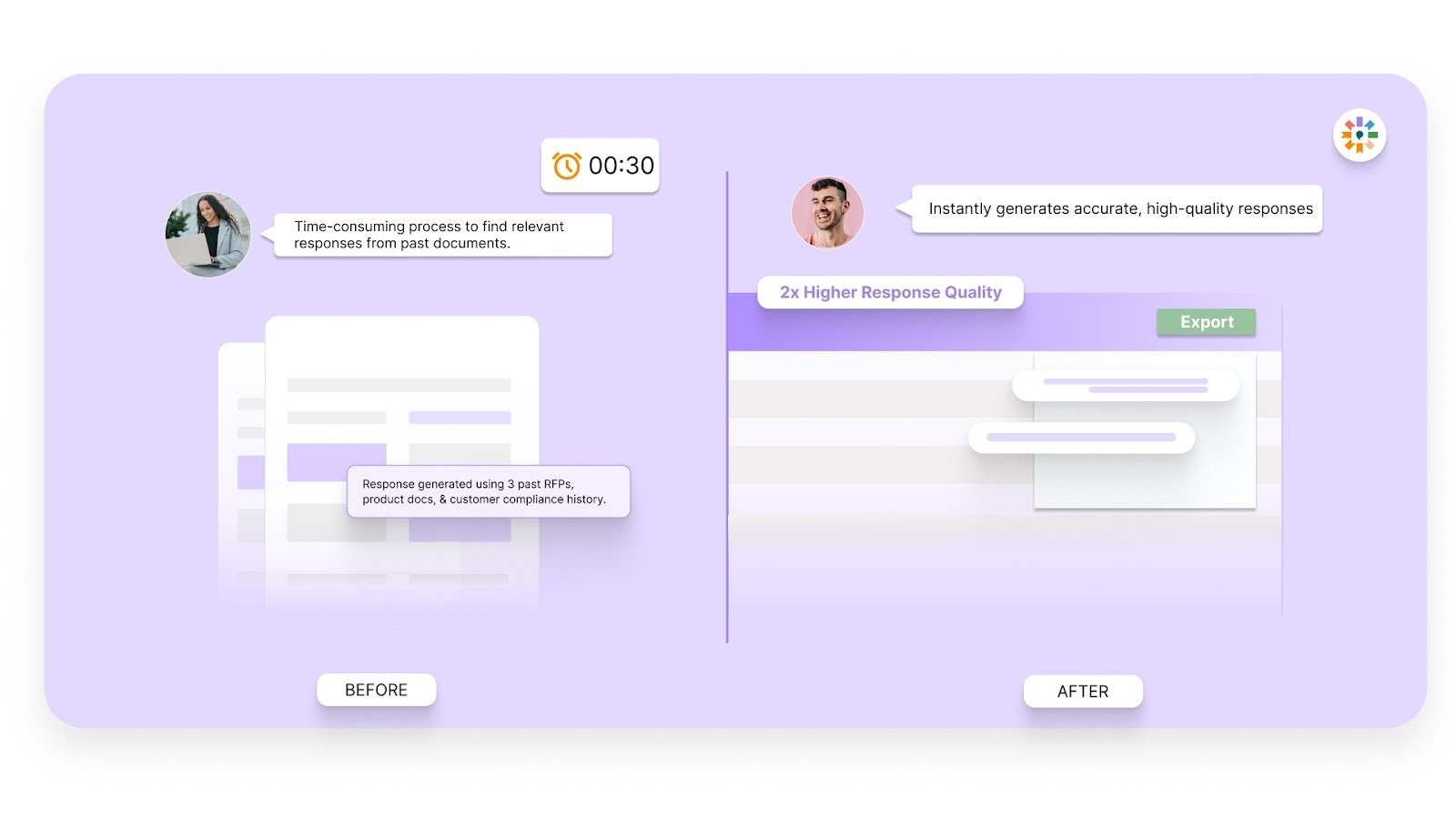
Inventive AI uses advanced AI algorithms to automatically draft responses with greater accuracy and depth. By analyzing historical data, it produces high-quality, detailed responses that align with your company’s security protocols and buyer expectations.
2. Context-Awareness
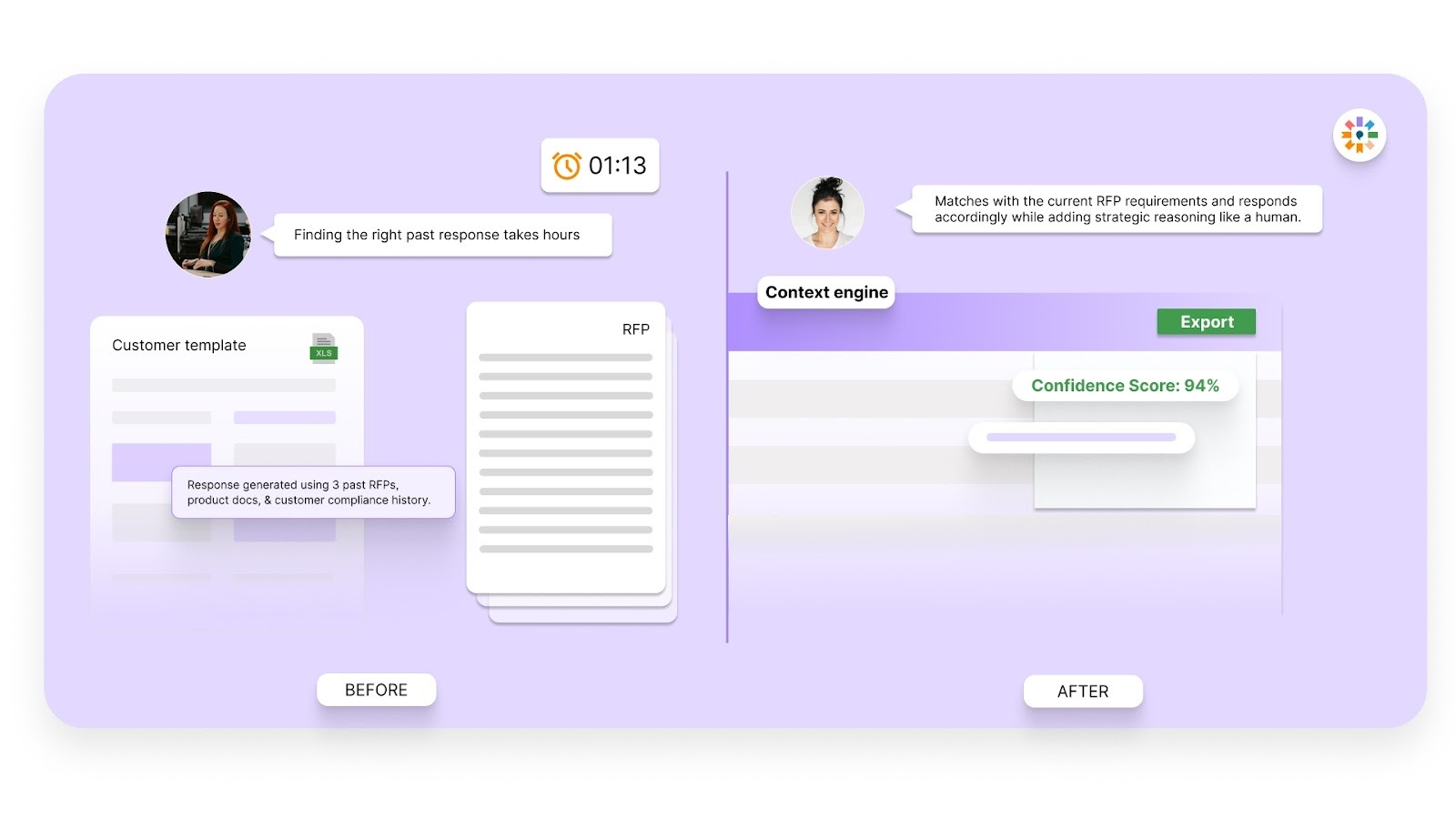
With context-aware technology, Inventive AI tailors each response to the specific needs of the buyer and their industry. Whether you're dealing with healthcare, finance, or government, Inventive AI ensures that every answer is relevant, specific, and compliant with industry regulations.
3. Instant Conflict Detection
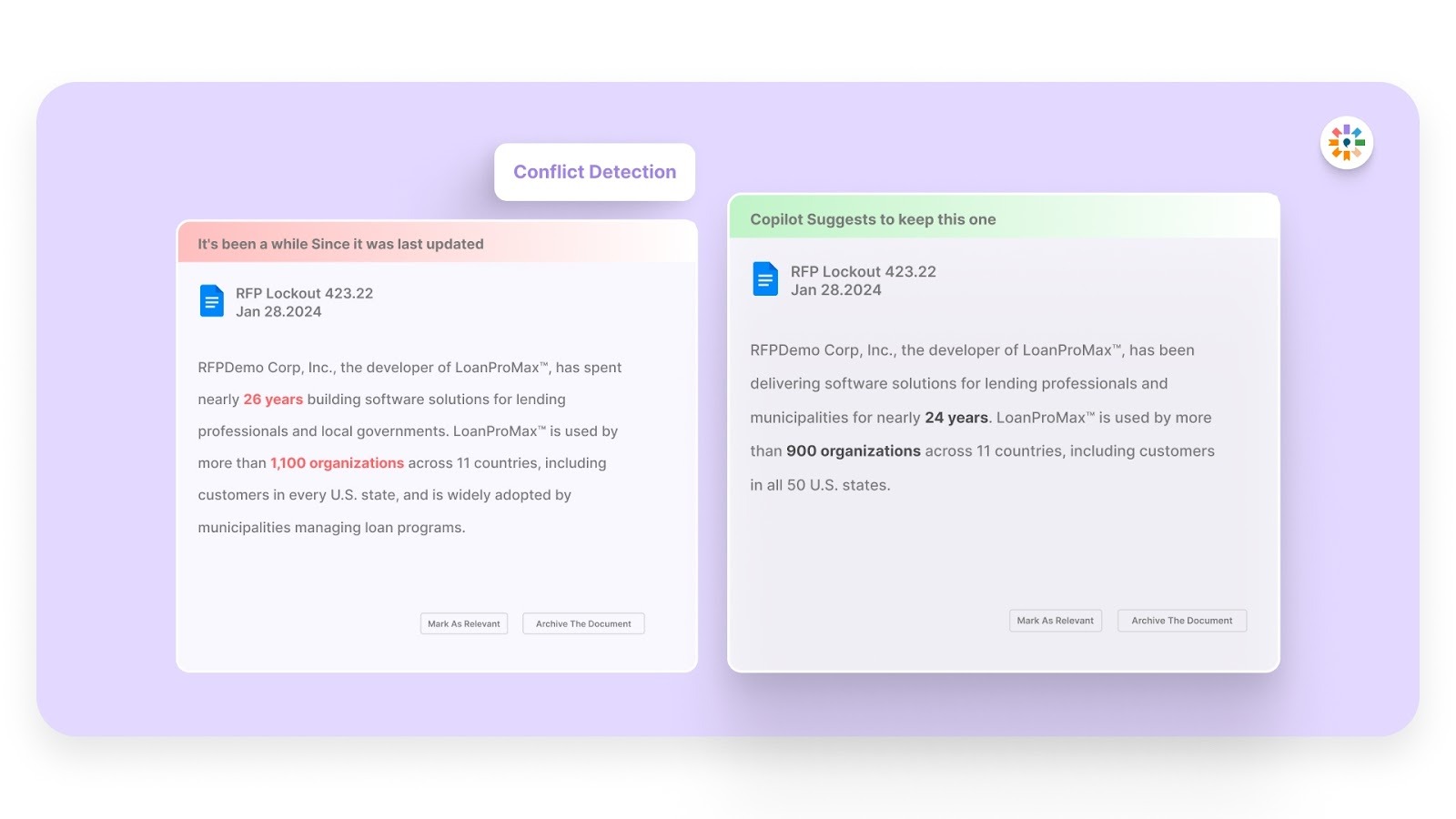
One of the biggest challenges in DDQ responses is the inconsistency of information. Inventive AI instantly identifies any conflicting or outdated content, helping you avoid errors and ensuring that all the information is aligned before submission. This reduces the riskk of delays caused by revisions and improves proposal quality.
4. Outdated Content Detection
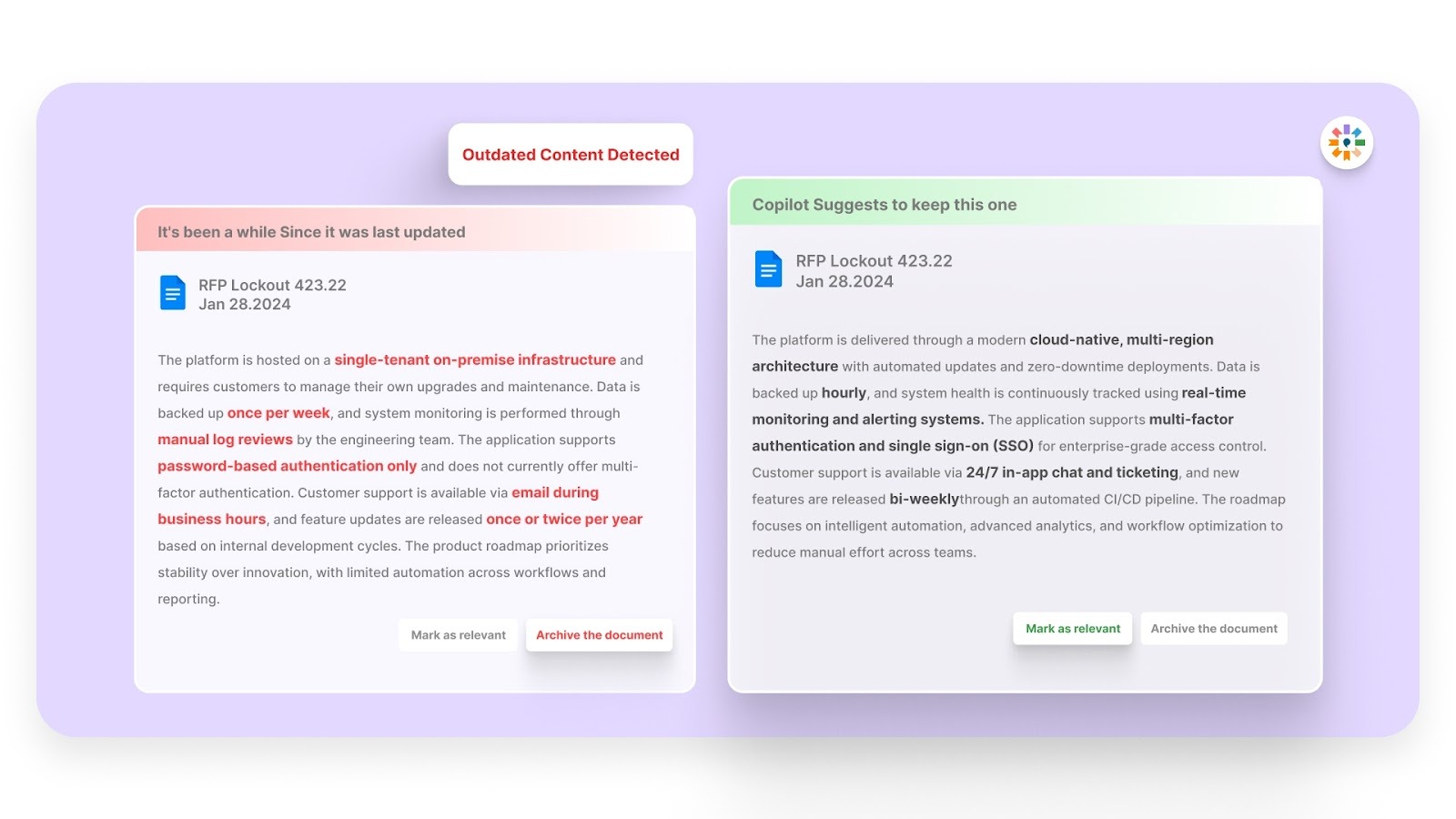
Cybersecurity practices and regulations change frequently. Inventive AI proactively flags any outdated content in your responses, ensuring that your answers are always up to date with the latest compliance standards and best practices in cybersecurity. This helps you maintain the accuracy and reliability of your responses.
5. Quality Benchmarking
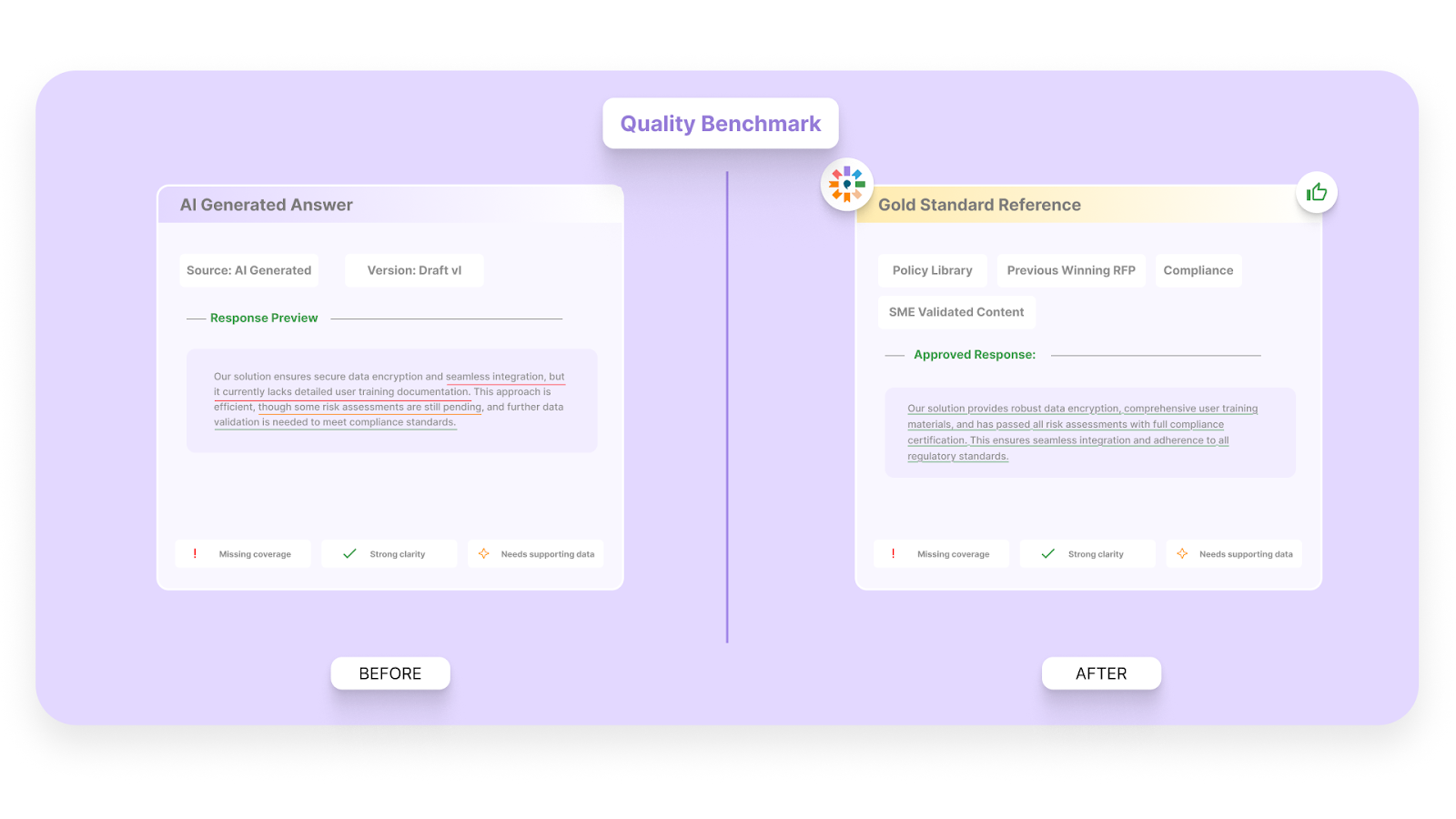
Maintain consistency across all your responses with quality benchmarking. Inventive AI compares your DDQ responses against a set of internal standards to ensure they meet your company’s security protocols and maintain a high standard of clarity and professionalism.
6. Narrative-Style Proposals
Rather than delivering fragmented, disconnected answers, Inventive AI turns your responses into cohesive, narrative-style proposals. This makes your answers more compelling, easier to follow, and more likely to resonate with potential buyers, ensuring that your proposal stands out in a competitive market.
7. Simple, Easy-to-Use Interface
Inventive AI's interface is intuitive and role-based, making it easy for security, legal, sales, and compliance teams to contribute without training overhead. This reduces internal friction, speeds up reviews, and keeps every stakeholder aligned on a single, trusted version of the response.
With Inventive AI, you can significantly speed up your DDQ response process while improving the accuracy and quality of your submissions. By automating manual tasks, eliminating outdated information, and ensuring consistency, Inventive AI helps you respond faster, win more deals, and build stronger relationships with your clients.
Frequently Asked Questions (FAQs)
1. How detailed should a cybersecurity DDQ response be?
DDQ responses should be precise, evidence-backed, and scoped to the question asked. Overly long answers raise review effort, while vague answers trigger follow-ups or disqualification. Buyers look for clarity, proof, and consistency more than volume.
2. How often should vendors update their DDQ answers?
DDQ responses should be reviewed at least quarterly or after any major security, compliance, or infrastructure change. Outdated answers around certifications, controls, or vendors are a common reason for delayed approvals.
3. Can incomplete DDQ responses block a deal even after a strong RFP?
Yes. Many deals stall or fail during security review if DDQs reveal gaps, inconsistencies, or missing documentation. DDQs often act as a final risk gate before contracts are approved.
4. Do buyers compare DDQ responses across vendors?
Absolutely. DDQs are scored side by side, especially in regulated industries. Inconsistent structure, unclear wording, or missing evidence makes comparison harder and lowers trust in the vendor’s security maturity.
5. What teams should be involved in preparing cybersecurity DDQs?
Effective DDQ responses usually involve security, compliance, legal, IT, and proposal teams. Without coordination, responses often conflict or rely on outdated information, increasing review cycles and buyer scrutiny.

90% Faster RFPs. 50% More Wins. Watch a 2-Minute Demo.
Understanding that sales leaders struggle to cut through the hype of generic AI, Mukund focuses on connecting enterprises with the specialized RFP automation they actually need at Inventive AI. An IIT Jodhpur graduate with 3+ years in growth marketing, he uses data-driven strategies to help teams discover the solution to their proposal headaches and scale their revenue operations.
Knowing that complex B2B software often gets lost in jargon, Hardi focuses on translating the technical power of Inventive AI into clear, human stories. As a Sr. Content Writer, she turns intricate RFP workflows into practical guides, believing that the best content educates first and earns trust by helping real buyers solve real problems.

.avif)
