Complete Guide to Security Questionnaire Templates for Fintech
Have you ever struggled to collect the right details for a security questionnaire? For issuers, it’s about gathering accurate information from vendors, and for vendors, it’s about providing clear, consistent answers under tight deadlines. Even missing one key detail can lead to delays and unnecessary follow-ups.
The answer? A well-organized security questionnaire template. With a clear template, you can save time, avoid mistakes, and make sure all the important details are covered. This guide will show you how a solid template can simplify your process. Plus, we’ll understand how AI-powered tools can make your responses even faster and more accurate.
Security Questionnaire Template for Fintech: Key Questions for Evaluating Vendors (for Buyers)

Using a security questionnaire template helps fintech companies respond quickly, accurately, and consistently to client assessments, ensuring your business meets necessary security and compliance standards.
Fintech Security Questionnaire Response Template: Your Key to Effortless Responses (for Vendors)

Key Components of a Security Questionnaire Template for Fintech
A well-structured security questionnaire template for fintech companies should cover the following key areas:
1. General Information & Governance
- Company Overview: Basic company details and the structure of your security program.
- Security Team: Information about the personnel responsible for security, their roles, and their experience.
2. Data Protection & Privacy
- Data Encryption: How do you protect data both at rest and in transit?
- Access Control: Who can access sensitive information and under what circumstances?
- Data Retention & Disposal: Policies around how long data is stored and how it’s securely disposed of.
3. Risk Management
- Risk Assessment: Outline your approach to risk management, including the identification and mitigation of risks.
- Incident Response: Your procedures for handling data breaches or security incidents.
4. Compliance
- Regulatory Standards: What security standards and compliance regulations do you meet (e.g., SOC 2, ISO 27001, GDPR, PCI-DSS)?
- Audit Reports: Provide any relevant security audit reports and certifications.
5. Vendor & Third-Party Risk
- Third-Party Vendor Management: How do you evaluate and manage third-party vendors with access to sensitive data?
- Subcontractor Oversight: How do you ensure that your subcontractors meet the same security standards?
A well-rounded security questionnaire template ensures that all critical areas, from data protection to compliance, are covered effectively, helping fintech companies demonstrate their security measures and commitment to best practices.
To help you understand how to respond to these key areas, we’ve created a downloadable security questionnaire template (from the buyer's side) that you can refer to when preparing your response.
This template will guide you through each section, making it easier to organize your answers and meet industry requirements.
Also Read: How to Create an Effective RFP Response
The Importance of Security Questionnaires in Fintech
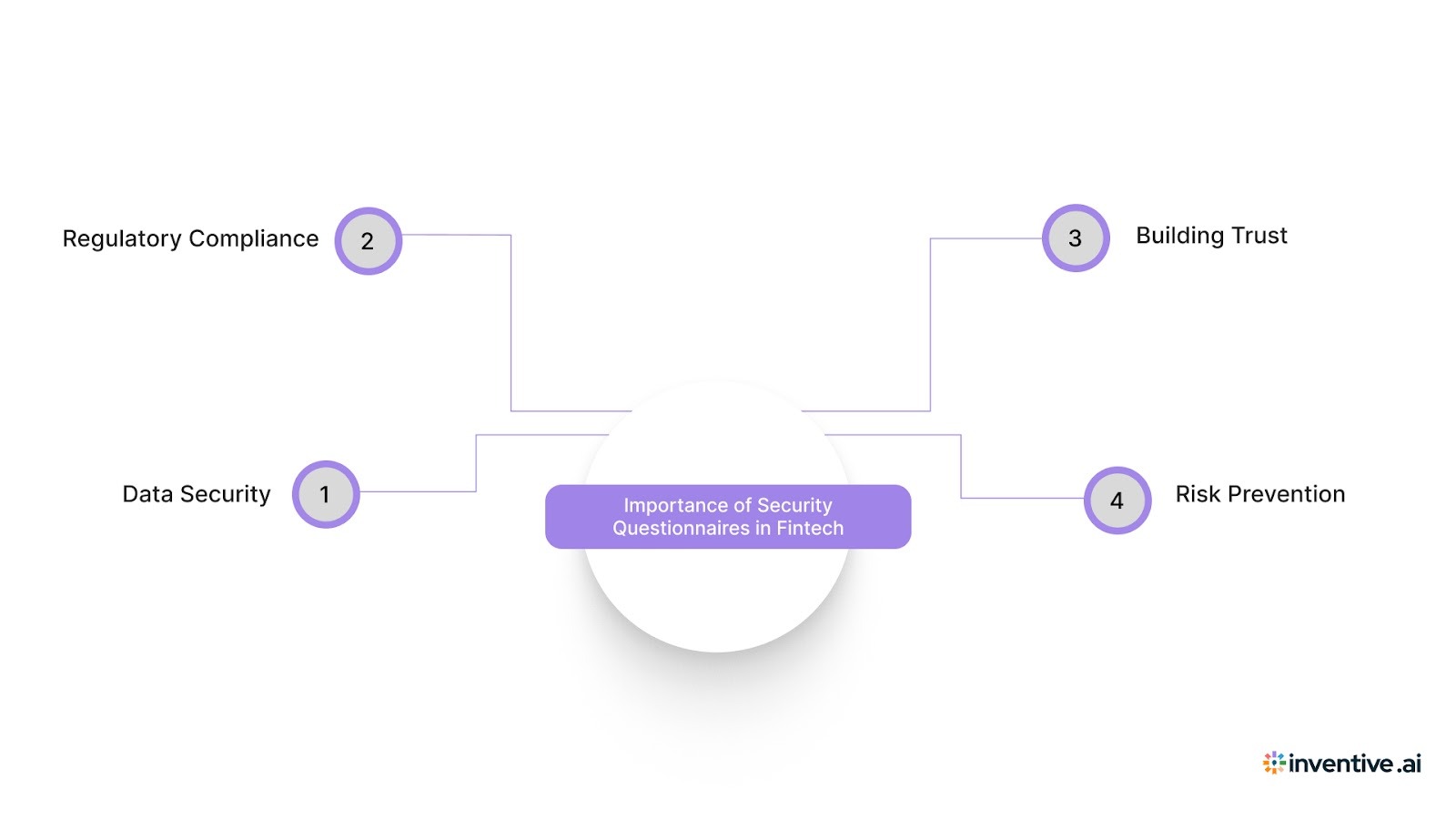
Fintech companies handle highly sensitive financial and personal data, which makes them prime targets for cyberattacks. Here’s why these questionnaires are particularly important for fintech companies:
1. Data Security: Protecting Sensitive Information
In the fintech industry, customer data is the most valuable asset, and any breach can lead to devastating financial, legal, and reputational consequences. Security questionnaires ask vendors detailed questions about how they secure sensitive data, from encryption protocols to data storage and transfer mechanisms.
Answering these questions thoroughly demonstrates your commitment to protecting client data and securing sensitive financial transactions.
Examples of Security Measures Covered:
- Data encryption standards (e.g., AES-256).
- Methods of access control and user authentication.
- How data is stored, both in transit and at rest.
These answers help ensure that your company is taking the necessary precautions to protect data from breaches, leaks, or unauthorized access.
2. Regulatory Compliance: Meeting Industry Standards
Fintech companies must comply with numerous regulatory frameworks that govern how financial data is handled and stored. These include GDPR (General Data Protection Regulation), PCI-DSS (Payment Card Industry Data Security Standard), SOC 2, and other region-specific regulations.
Security questionnaires evaluate how vendors adhere to these regulations and standards, ensuring that you are partnering with compliant organizations.
Key Compliance Areas Assessed:
- Data handling and privacy practices.
- Compliance with GDPR for EU data.
- Adherence to PCI-DSS for handling payment information.
- SOC 2 reports, which assess a company’s controls over data security, availability, processing integrity, confidentiality, and privacy.
By responding to these questions, you show that your company is prepared to meet regulatory standards, reducing legal and financial risks.
3. Trust: Building Confidence with Clients and Partners
In a sector where clients are entrusting you with sensitive financial information, trust is paramount. Clients and partners want assurance that their data is secure, and that your company adheres to strict data protection policies.
A well-prepared response to security questionnaires builds confidence with potential clients and partners, showing that you take data security seriously and have established practices to protect their information.
Building Trust:
- Demonstrates due diligence in selecting secure, compliant vendors.
- Reinforces your commitment to transparency and proactive security measures.
- Establishes credibility, especially with new or prospective clients who may not yet be familiar with your security practices.
In essence, a properly completed security questionnaire is not just about passing an evaluation; it’s about establishing trust and showcasing your company's dedication to security and compliance.
4. Avoiding Financial & Reputational Damage
The financial and reputational impact of a data breach can be significant. Beyond fines and penalties for non-compliance, a breach can erode customer trust and damage relationships with partners.
By completing security questionnaires thoroughly and accurately, you help demonstrate that your business has the right processes in place to mitigate these risks, making it less likely that a security lapse will happen.
Real-World Impact:
- The average cost of a data breach in the financial sector is estimated to be $5.85 million (source: IBM, 2020).
- A breach can cause long-term reputational damage, with clients choosing to leave for competitors with more secure practices.
Answering security questionnaires correctly shows your clients and partners that you prioritize data security, compliance, and risk management. While these questionnaires help mitigate risks, they also allow you to demonstrate your fintech company’s commitment to protecting sensitive information.
Also Read: How AI in Presales is Redefining Speed, Accuracy, and Win Rates
7 Tips to Maximize the Impact of Your Security Questionnaire Template
Customizing your security questionnaire template is essential to ensure that your responses resonate with potential clients and demonstrate your commitment to meeting their security needs.
Here are 7 tips to help you get the most out of your template and create impactful, relevant responses.
1. Tailor the Introduction to Address the Client’s Priorities: Start by aligning your introduction with the client’s key security concerns. Highlight how your solutions match their specific needs, setting the tone for the rest of the questionnaire.
2. Emphasize the Most Relevant Security Practices: Focus on the security measures and practices that are most important to the client. Whether it's encryption, access control, or incident response, make sure you highlight what matters most to them.
3. Align Your Approach to the Client’s Expectations: Modify your responses based on what the client is looking for. For example, if they emphasize compliance, make sure to showcase your adherence to relevant regulations like GDPR or SOC 2.
4. Adapt Your Response to Their Timeline: If the client has a tight deadline, focus on your ability to meet their schedule and highlight any fast implementation processes or previous success with rapid deployments.
5. Showcase Your Key Strengths Based on Client Needs: Demonstrate what sets your security practices apart by tailoring responses to address the client’s specific concerns, whether it’s advanced data encryption or robust third-party risk management.
6. Adjust Your Pricing Structure to Match Client Requirements: If applicable, provide a pricing structure that is flexible or tailored to the client's needs. Highlight the value of your security practices relative to the costs.
7. Keep Your Response Focused and Easy to Understand: Ensure your answers are direct, easy to follow, and free of jargon. Clients should be able to quickly understand your security measures and their benefits.
By customizing your security questionnaire template, you align your response with the client’s unique needs and priorities, ensuring your solution stands out and builds trust.
AI for Security Questionnaires: The Future of Efficient Responses
Responding to security questionnaires can be a complex and time-consuming task, with multiple questions, data management needs, and compliance requirements to address. However, AI-powered tools can help simplify this process by automating key steps, reducing manual work, ensuring accuracy, and helping you stay compliant with the latest standards.
Key Features of AI-Powered Tools for Security Questionnaires
- Automated Drafting: AI can instantly generate initial drafts based on historical responses and internal documentation, saving valuable time and effort.
- Real-Time Updates: AI tools automatically flag outdated content, ensuring your responses are always current and compliant with the latest regulations and industry standards.
- Accuracy & Consistency: AI helps ensure that your responses are consistent across different documents and align with your company’s messaging, reducing the risk of errors.
- Seamless Collaboration: AI-powered tools enable more efficient collaboration among teams, ensuring that all contributors are aligned and working from the same up-to-date information.
Inventive AI: The Key to High-Quality, Consistent Security Questionnaire Responses
Responding to security questionnaires often requires pulling answers from multiple documents, policies, and previous responses. Teams spend hours searching for the right information, validating it, and making sure the response is accurate.
Inventive AI simplifies this process by helping you generate consistent, reliable responses while keeping your knowledge organised and up to date.
Here is how Inventive AI supports security questionnaire responses.
1. 2× Higher Quality Responses
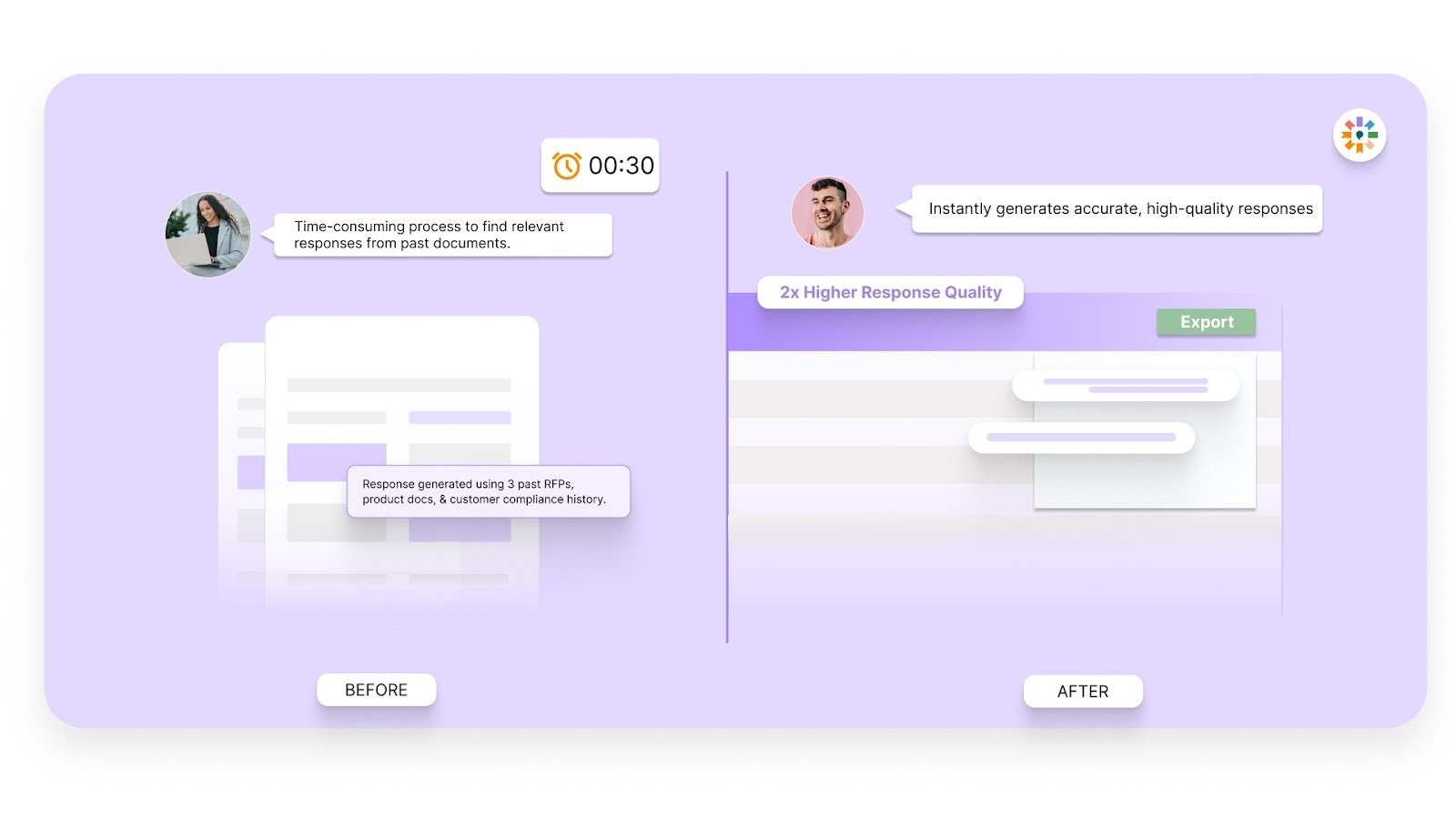
Inventive AI improves the quality of responses by referencing approved company documents, past answers, and security policies.
Instead of manually rewriting answers each time, you generate responses that remain consistent, detailed, and aligned with your organisation’s standards.
2. Context Engine
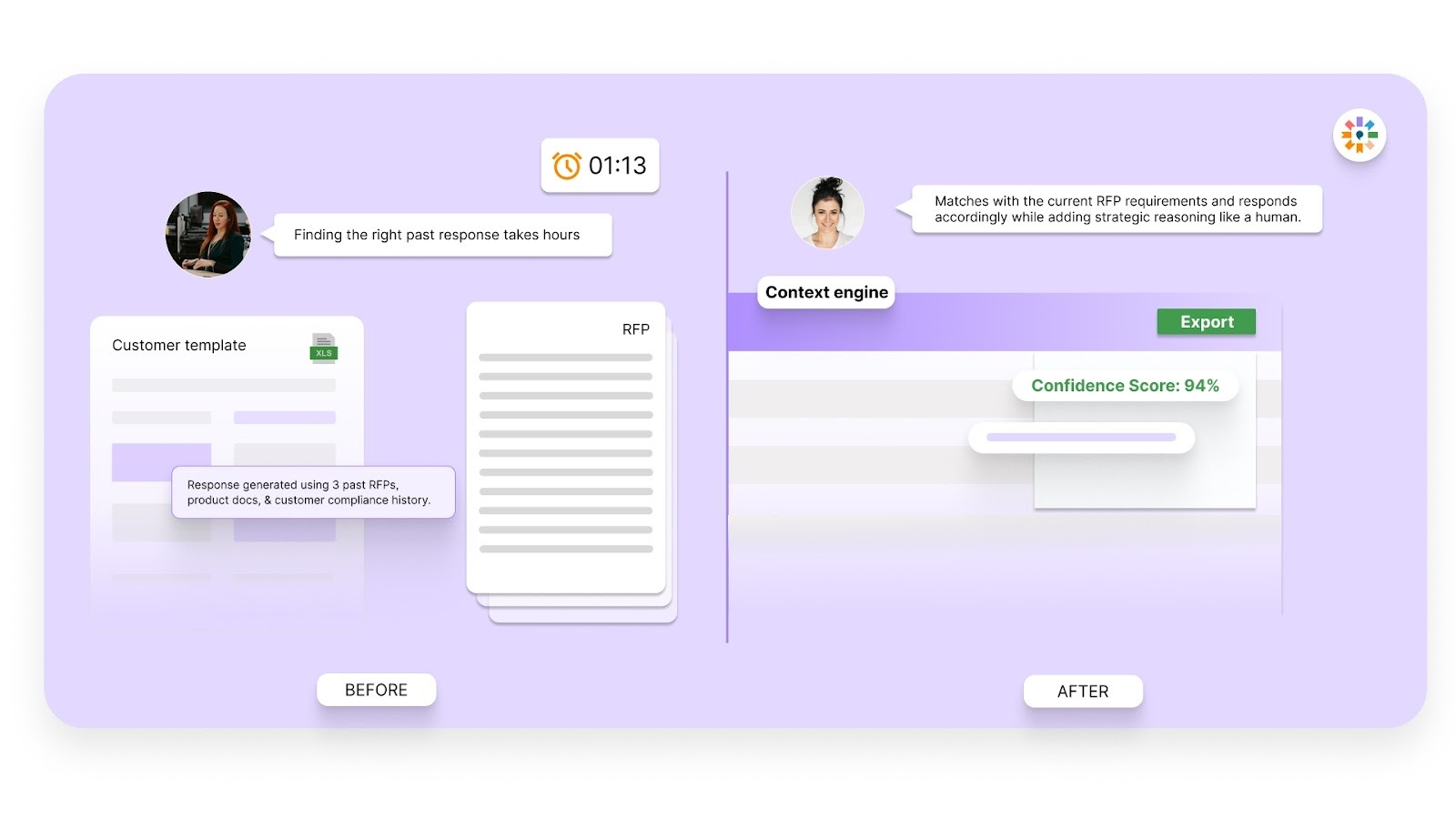
Inventive AI’s context engine understands the intent behind each question and retrieves the most relevant information from your knowledge base.
This allows the system to produce responses that reflect your organisation’s policies, certifications, and security practices.
3. Conflict Detection
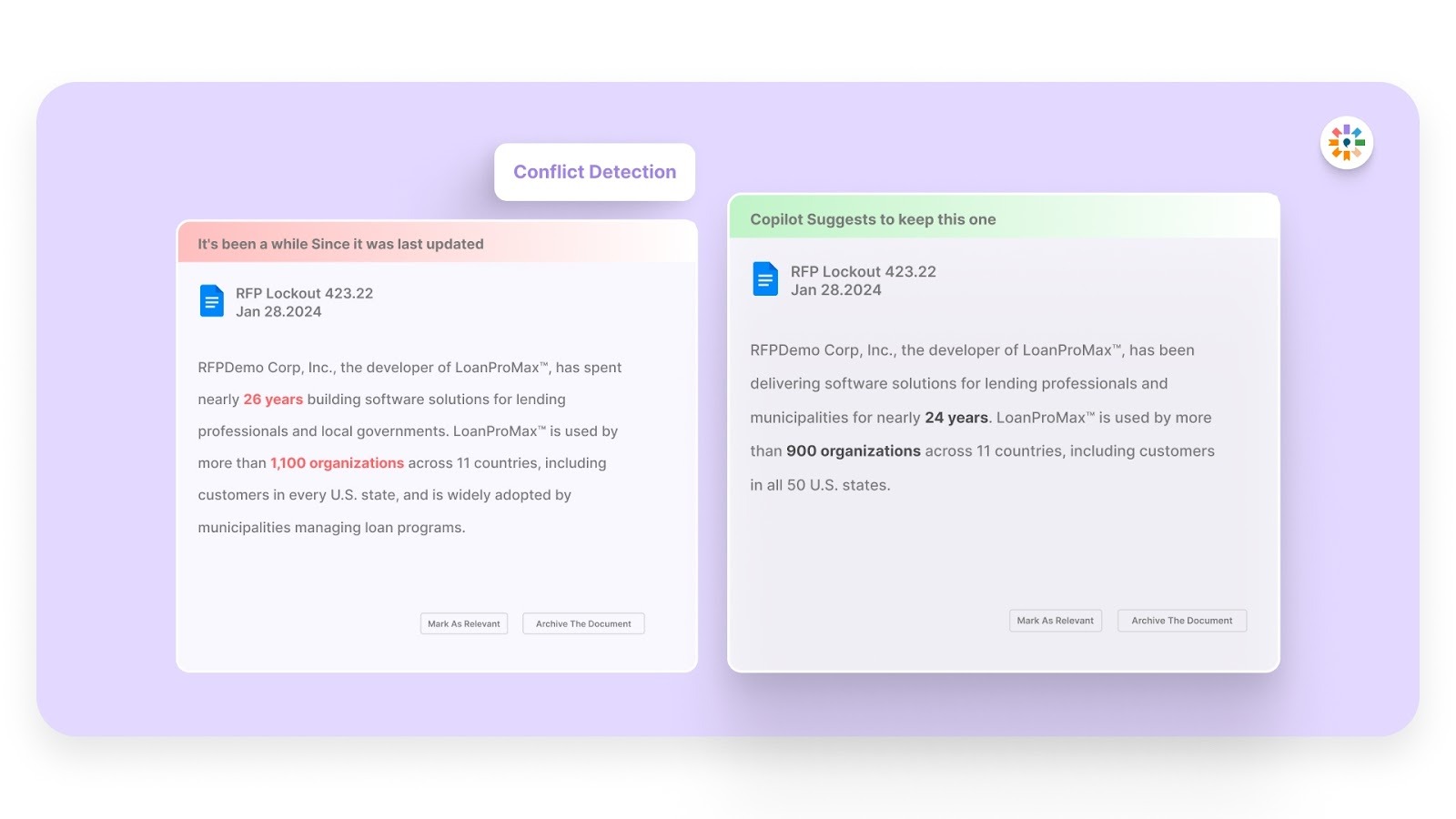
Security responses must remain consistent across questionnaires. Inventive AI identifies conflicting information across previous answers and highlights it before submission.
This helps prevent contradictory responses that can raise concerns during vendor security reviews.
4. Outdated Content Detection
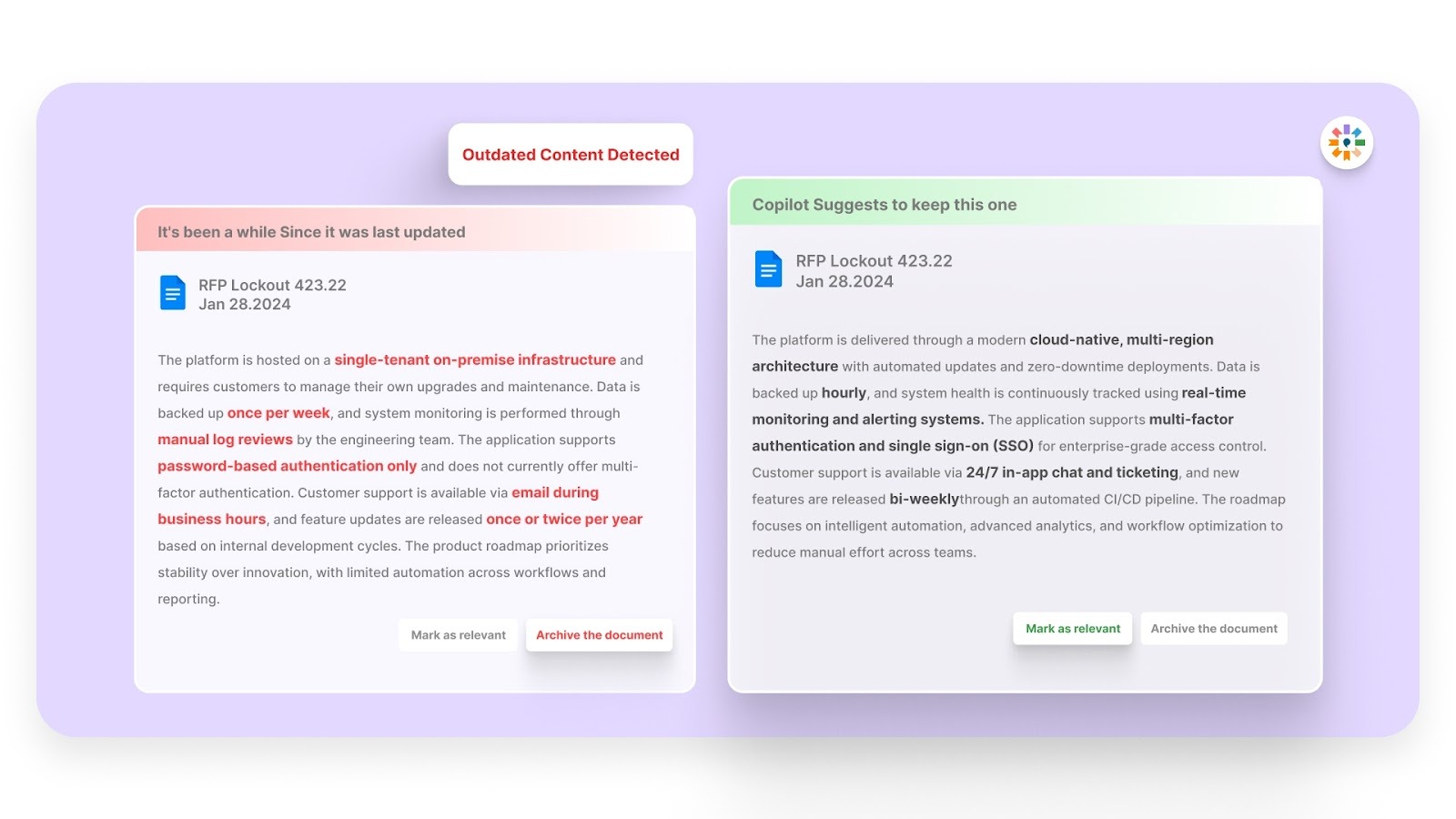
Security policies and certifications change over time. Inventive AI flags outdated answers so your team can update them before they are reused.
This ensures that every questionnaire reflects the most recent information about your security practices.
5. Simple, Easy-to-Use Interface
Inventive AI is designed for security, compliance, and proposal teams who need to move quickly.
The platform makes it easy to upload documents, organise knowledge, generate answers, and review responses without complex workflows.
6. Narrative-Style Proposals
Win over stakeholders with polished, executive-ready content. Inventive AI transforms complex RFP data into clear, long-form summaries and briefs, ensuring your most important value propositions are front and center for decision-makers.
With structured knowledge, accurate responses, and faster completion times, Inventive AI helps organisations handle security questionnaires with greater confidence and consistency.
Frequently Asked Questions (FAQs)
1. How often should vendors update their security questionnaire responses?
Vendors should update their responses annually or whenever there are changes in security practices, compliance requirements, or new regulatory standards that impact their solution.
2. What’s the best way to present sensitive data security measures in an RFI or security questionnaire?
Be clear and detailed when explaining your data security practices. Describe the encryption standards used (e.g., AES-256, TLS 1.2/1.3), how you control data access (e.g., MFA, SSO), and provide evidence of your certifications to show your commitment to securing sensitive data.
3. How do vendors prove compliance with regulatory standards in security questionnaires?
Vendors can prove compliance by providing relevant certifications (e.g., SOC 2, ISO 27001, GDPR) and audit reports that validate adherence to industry regulations. Be sure to explain how your solution meets or exceeds security protocols specific to fintech.
4. What are the key challenges vendors face when responding to fintech security questionnaires?
Vendors often face challenges in maintaining consistency across multiple submissions, gathering information from different teams, and staying up-to-date with changing compliance and security regulations.
5. How can vendors ensure their security questionnaire responses are complete and accurate?
Vendors should maintain a centralized knowledge base that includes the latest security policies, compliance certifications, and audit reports to ensure responses are accurate and consistent.

90% Faster RFPs. 50% More Wins. Watch a 2-Minute Demo.
Knowing that complex B2B software often gets lost in jargon, Hardi focuses on translating the technical power of Inventive AI into clear, human stories. As a Sr. Content Writer, she turns intricate RFP workflows into practical guides, believing that the best content educates first and earns trust by helping real buyers solve real problems.
After witnessing the gap between generic AI models and the high precision required for business proposals, Gaurav co-founded Inventive AI to bring true intelligence to the RFP process. An IIT Roorkee graduate with deep expertise in building Large Language Models (LLMs), he focuses on ensuring product teams spend less time on repetitive technical questionnaires and more time on innovation.


