HIPAA Security Risk Assessment: The Ultimate Checklist for Healthcare Organizations

As a healthcare professional, you’re probably no stranger to the constant pressure of ensuring HIPAA compliance while juggling day-to-day operations. The complexity of conducting accurate HIPAA Security Risk Assessments can be overwhelming, and it’s not uncommon for organizations to fall behind in this critical area. Unfortunately, failing to stay on top of risk assessments can lead to costly breaches, fines, and a damaged reputation.
In this blog, we’ll provide an updated checklist for HIPAA Security Risk Assessments in 2026 and show you how Inventive AI can help make this process quicker, more accurate, and more reliable.
Key Takeaways
- HIPAA Security Risk Assessments identify risks and vulnerabilities to Protected Health Information (PHI), helping ensure compliance with regulations.
- Regular risk assessments are important in 2026 to address evolving cyber threats and meet updated HIPAA requirements.
- Not conducting proper risk assessments can result in fines, data breaches, and a loss of patient trust.
- Inventive AI automates report creation, flags outdated content, and ensures real-time compliance, improving the speed and accuracy of assessments to stay ahead of emerging threats and maintain compliance through proactive risk management.
What is a HIPAA Security Risk Assessment Questionnaire?
The Health Insurance Portability and Accountability Act (HIPAA) is a U.S. law that ensures the protection of individuals' health information. It sets clear standards for maintaining the privacy and security of Protected Health Information (PHI), requiring healthcare organizations to implement strong security measures to prevent unauthorized access to sensitive data.
A HIPAA Security Risk Assessment (SRA) is an important process for healthcare providers. It helps you identify potential risks and vulnerabilities that could threaten the security of PHI. The purpose of this assessment is to evaluate whether current policies, procedures, and security measures are adequate to protect PHI and minimize risks to an acceptable level.
As healthcare organizations work to meet increasingly complex regulatory requirements, it's important to understand that the quality of responses in risk assessments plays a crucial role in both data security and compliance. Weak, outdated, or inconsistent answers can lead to serious consequences, such as compliance failures, data breaches, and a loss of patient trust.
Why a HIPAA Security Risk Assessment Questionnaire is Important for Healthcare Organizations in 2026?
If you sell software or services to healthcare providers, you will likely be asked to answer HIPAA security and compliance questionnaires during vendor evaluations. Healthcare organizations use these assessments to check whether vendors can safely handle Protected Health Information (PHI).
As cyber threats increase and compliance requirements change, healthcare buyers review vendor security practices more closely. Your responses to HIPAA Security Risk Assessment (SRA) questions need to be clear, accurate, and consistent.
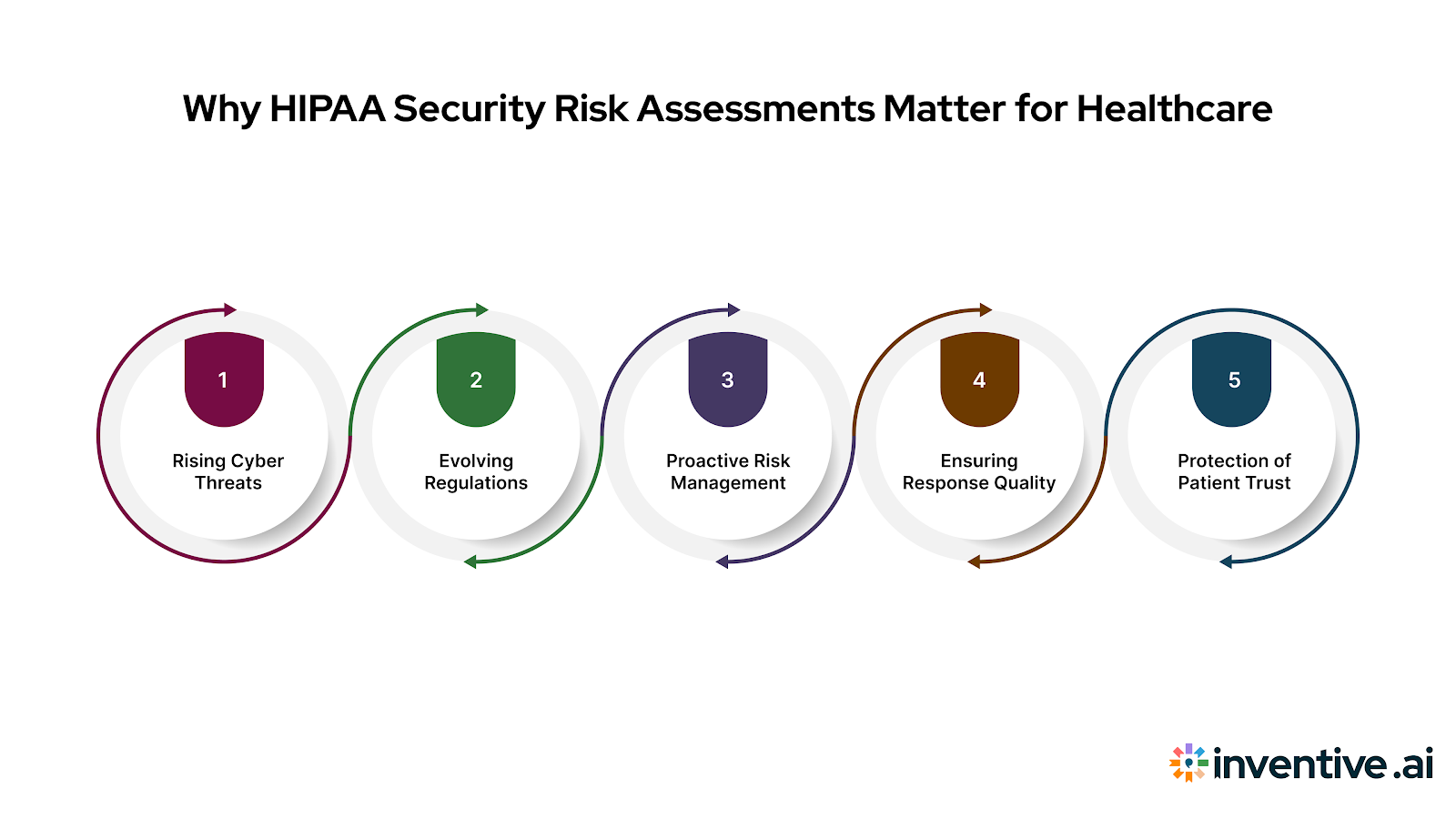
Here’s why a HIPAA Security Risk Assessment questionnaire is important in 2026:
1. Rising Cyber Threats
Healthcare organizations are frequent targets for cyberattacks. Because vendors often connect to hospital systems or handle sensitive data, buyers carefully review vendor security practices.
A detailed SRA helps healthcare organizations identify risks that could expose electronic Protected Health Information (ePHI). Your responses help show how your systems protect this data.
2. Evolving Regulations
HIPAA requirements and healthcare privacy rules continue to change. Healthcare organizations must keep their compliance programs updated, which means vendors are often asked for updated security documentation.
If your responses include outdated or inconsistent information, it can create compliance concerns during vendor reviews.
3. Proactive Risk Management
Healthcare organizations aim to identify risks before incidents occur. As part of this process, they review how vendors manage security risks within their systems.
Your responses to HIPAA assessments help buyers understand how your organization detects, manages, and reduces security risks.
4. Response Quality Matters
Healthcare organizations carefully review vendor responses during security assessments. Incomplete or inconsistent answers can slow down procurement or trigger additional reviews.
Platforms like Inventive AI help vendors maintain accurate and consistent responses by organizing security documentation and flagging outdated content.
5. Protecting Patient Trust
Healthcare organizations conduct these assessments to protect patient data. Vendors that provide clear and well-documented responses help build trust during security reviews.
Strong responses show that your systems can safely handle sensitive healthcare data.
As healthcare organizations strengthen security requirements in 2026, vendor security reviews are becoming more detailed. Preparing accurate HIPAA risk assessment responses helps you pass these evaluations faster and build trust with healthcare buyers.
Who Performs HIPAA Security Risk Assessments Questionnaire?
If you sell software or services to healthcare organizations, you will likely encounter HIPAA security risk assessments during vendor reviews.
Healthcare buyers use these assessments to check whether vendors can safely handle Protected Health Information (PHI).
Several groups are usually involved in performing or reviewing these assessments.
1. Healthcare Organizations
Hospitals, clinics, and health insurers perform HIPAA Security Risk Assessments to identify risks to electronic Protected Health Information (ePHI).
During vendor evaluations, they may ask vendors questions about security controls, data protection, and system access.
2. Business Associates
Vendors that store, process, or access PHI are considered business associates under HIPAA.
If your product handles healthcare data, you may be asked to provide documentation or answer security questionnaires as part of the healthcare organization’s risk assessment process.
3. Internal Security and Compliance Teams
Healthcare organizations usually have internal security or compliance teams that review vendor responses.
They evaluate whether your security practices meet their HIPAA requirements before approving your product or service.
4. Third-Party Security Assessors
Some healthcare organizations hire external cybersecurity firms or compliance consultants to conduct independent assessments.
These assessors may review vendor documentation and request evidence to verify security practices.
Because multiple stakeholders review HIPAA risk assessments, vendors need clear and consistent responses to pass security reviews smoothly.
Also Read: Top 5 RFP Software in 2026: Which to Use?
The Updated 2026 HIPAA Security Risk Assessment Questionnaire Checklist
To stay compliant and reduce security risks, healthcare organizations must take a comprehensive approach to HIPAA Security Risk Assessments.
Here’s an updated checklist for 2026:
Regular HIPAA Security Risk Assessments are important to maintaining compliance and protecting patient data. By adopting proactive risk management strategies and using the right tools, you can ensure the safety of your organization’s sensitive information.
Also Read: Patient Engagement RFPs: How Healthcare Vendors Can Respond Faster and Win More Contracts?
7 Common Challenges in Responding to HIPAA Security Risk Assessments Questionnaire (And How You Can Fix It)
When healthcare organisations evaluate vendors, HIPAA security risk assessment questions are often part of the due diligence process. Even if you have solid security practices, responding can get messy.
Here are the most common challenges vendors run into, plus practical ways to fix them.
1. Scattered evidence across tools and folders
Security policies, compliance documents, audit reports, and architecture details are often stored across different tools or folders. This makes it difficult to quickly find the right information when answering questionnaires.
Maintain a single source of truth for security and compliance content (policies, controls, standard answers, supporting artefacts) with clear owners and versioning.
2. Inconsistent answers across questionnaires
You may describe the same control differently across RFPs, security questionnaires, and customer emails, especially when multiple people contribute. Healthcare buyers notice mismatches and ask follow-ups.
Standardize approved answers for repeat questions (encryption, MFA, backups, logging, access reviews, breach response, subcontractors) and reuse them with light tailoring for each buyer.
3. Outdated documentation creates red flags
An old policy date, a retired tool name, or a stale architecture diagram can undermine confidence, even if your current controls are strong.
Set a review cadence for core documents (security policies, risk management, incident response, BCP/DR, access control). Keep a simple last reviewed / next review tracker and update templates when tools or processes change.
4. Overpromising in answers
In a rush to pass a review, it’s easy to write absolute statements like “we never…” or “we always…”. If the buyer later asks for proof and you can’t support it, you end up in a risky back-and-forth.
Be precise and evidence-based. Describe what you do, how often, and where it’s documented (policy name, system report, audit log, ticket workflow). If something is partially implemented, say so and provide a timeline.
5. Explain your safeguards questions are time-consuming
Many questions require narrative answers (how you secure ePHI, how access is granted, how incidents are handled). Writing these repeatedly wastes time and increases inconsistency.
Create reusable control narratives (1–2 paragraphs each) for common areas: access control, encryption, logging/monitoring, vulnerability management, vendor management, and incident response.
6. Evidence packaging slows procurement
Healthcare organisations often ask for attachments (policies, audit summaries, diagrams, risk assessment summaries). If you can’t package evidence quickly, approvals drag.
Build an evidence pack folder structure with a standard index (what’s included, date, scope, and contact). Keep redaction-ready versions where needed.
7. Buyer requirements aren’t consistent
One healthcare organisation may ask for specific details (e.g., how you handle access reviews), while another focuses on subcontractors or encryption. You end up rewriting for each buyer.
Use a modular response set: a base answer + optional add-ons (more detail, evidence links, process steps). This lets you expand only when the buyer asks.
Use standard answers, updated documentation, and organized evidence to respond faster and avoid delays during healthcare vendor security reviews.
Also Read: Construction RFP Guide: How Winning Teams Respond
How Inventive AI Can Simplify Your HIPAA Security Risk Assessment Questionnaire Responses?
Responding to HIPAA security risk assessment questionnaires requires clear, accurate, and consistent answers. Vendors often need to gather information from different teams and documents, which can slow down the process.
Inventive AI helps simplify this by organizing your security information and helping you generate accurate responses faster. With up to 50% higher win rates and 66% of responses requiring no edits, Inventive AI simplifies the process, ensuring both speed and accuracy.
Here’s how Inventive AI helps vendors respond to HIPAA security assessments.
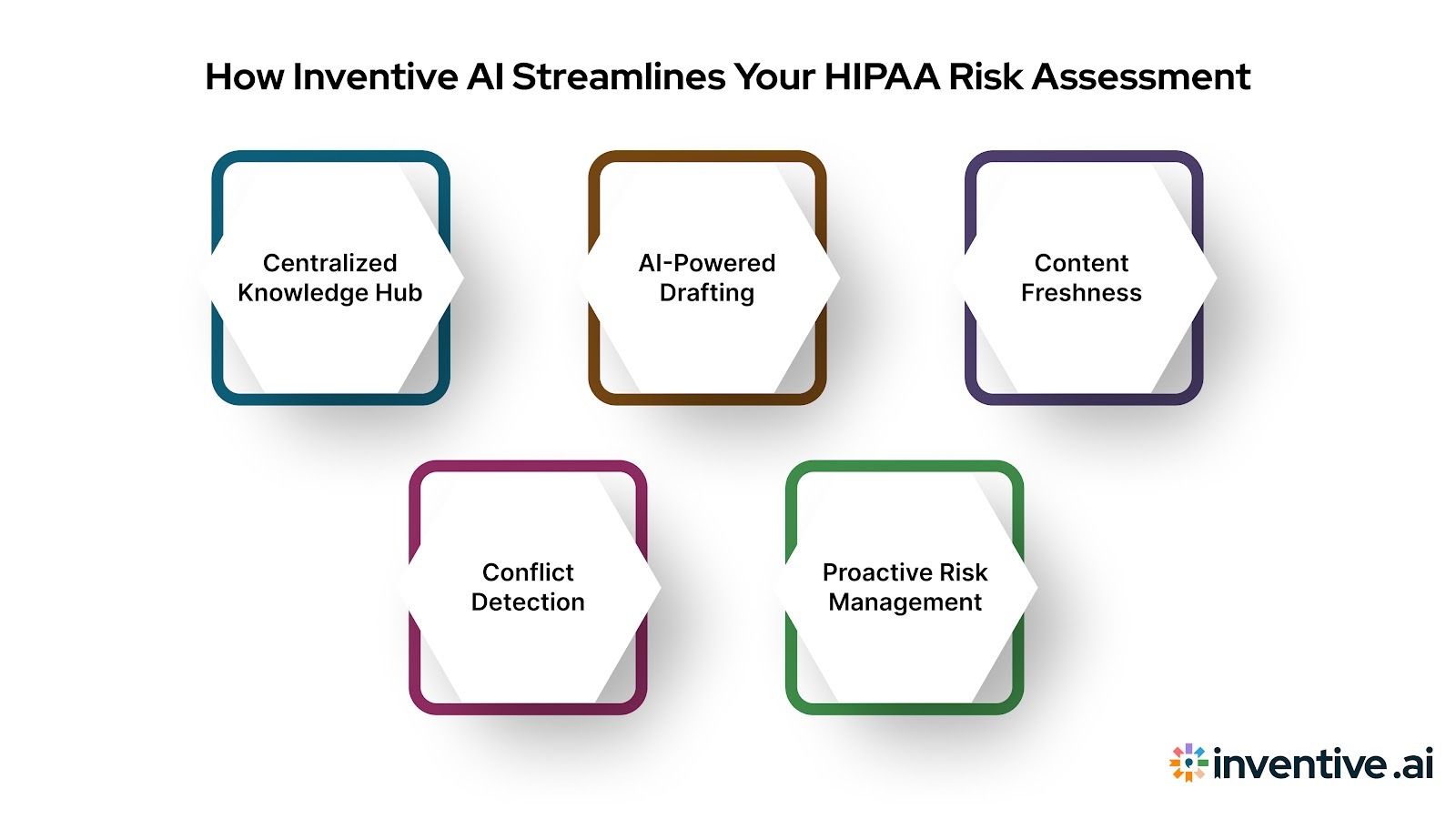
1. 2× Higher Quality Responses
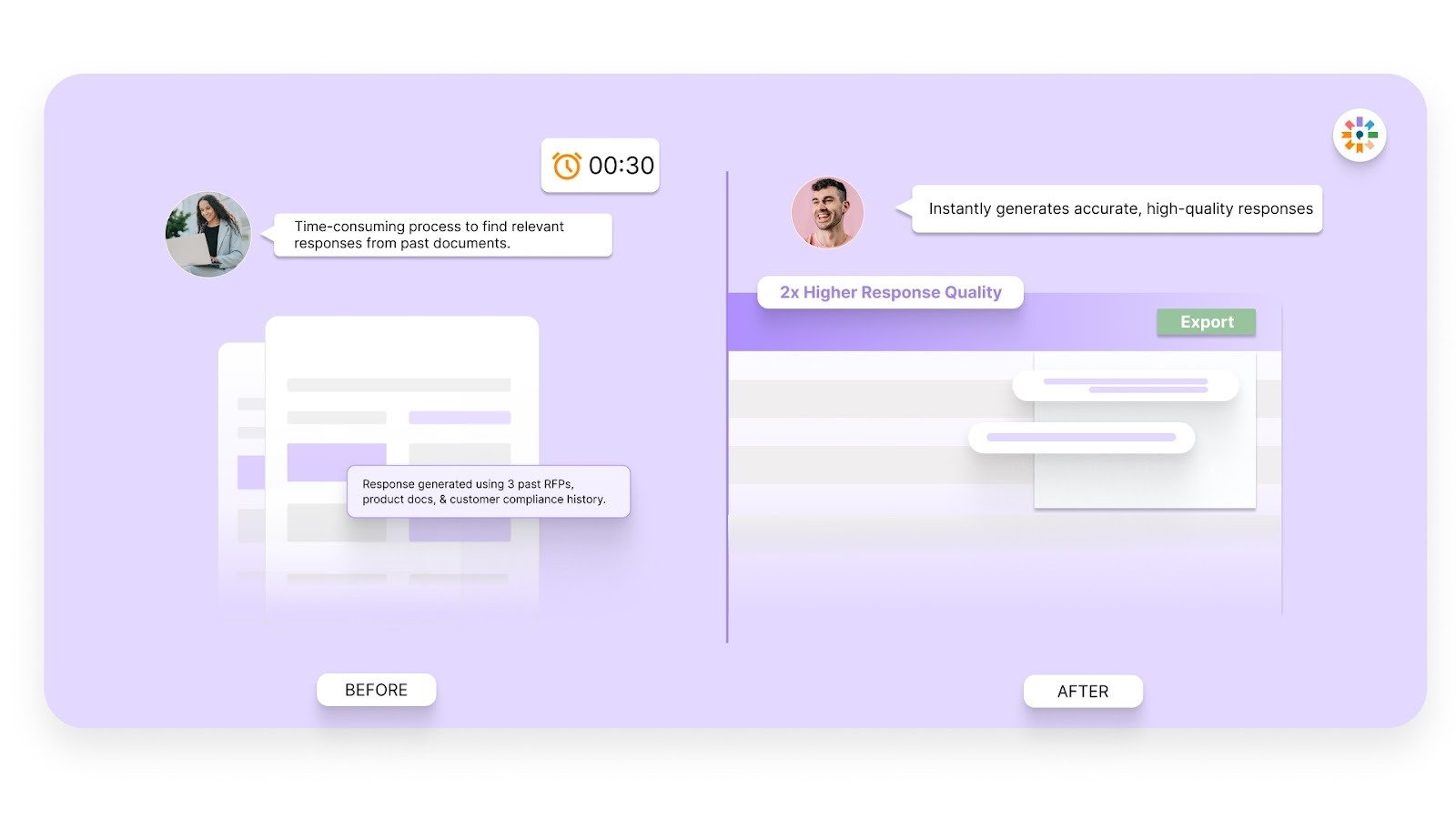
HIPAA questionnaires ask detailed questions about your security practices. Inventive AI uses your existing documentation and past responses to generate accurate answers that align with your security policies.
2. Context Engine
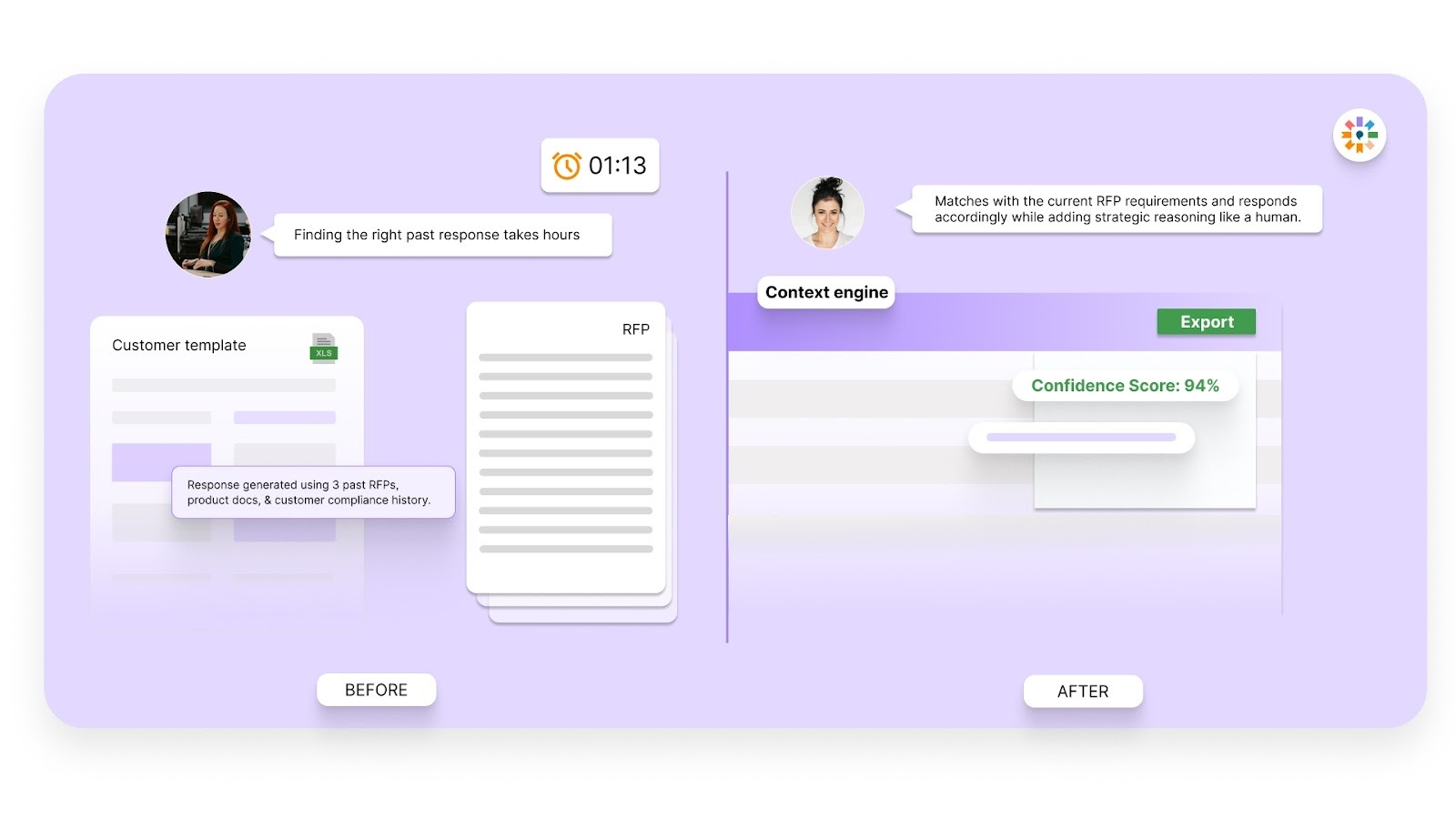
Security questionnaires often contain complex questions that require specific answers. Inventive AI’s Context Engine analyzes each question and pulls the most relevant information from your knowledge base to create clear and relevant responses.
3. Conflict Detection
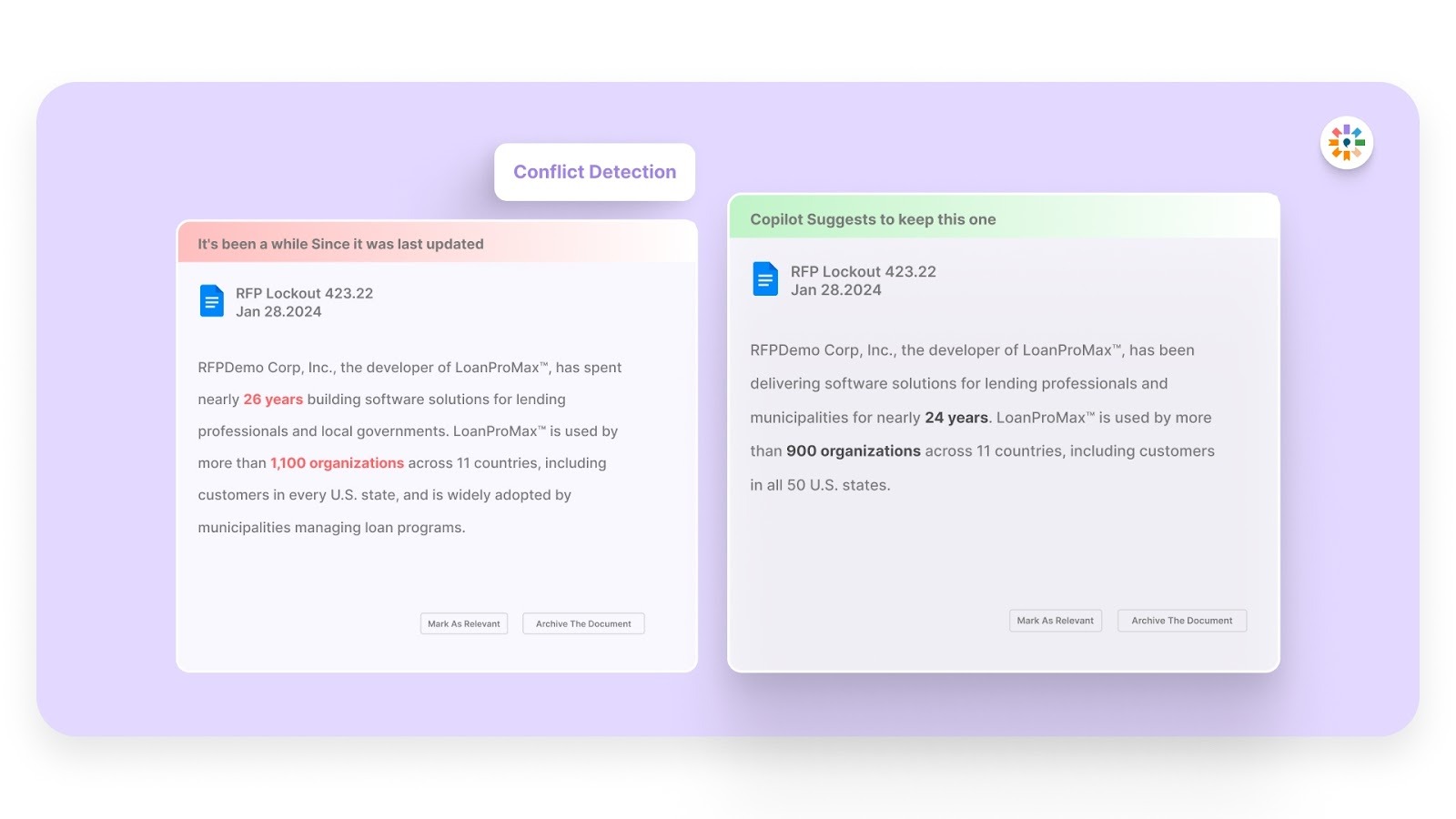
Inconsistent answers across questionnaires can raise concerns during vendor security reviews. Inventive AI detects conflicting responses and flags them so you can fix them before submitting your answers.
4. Outdated Content Detection
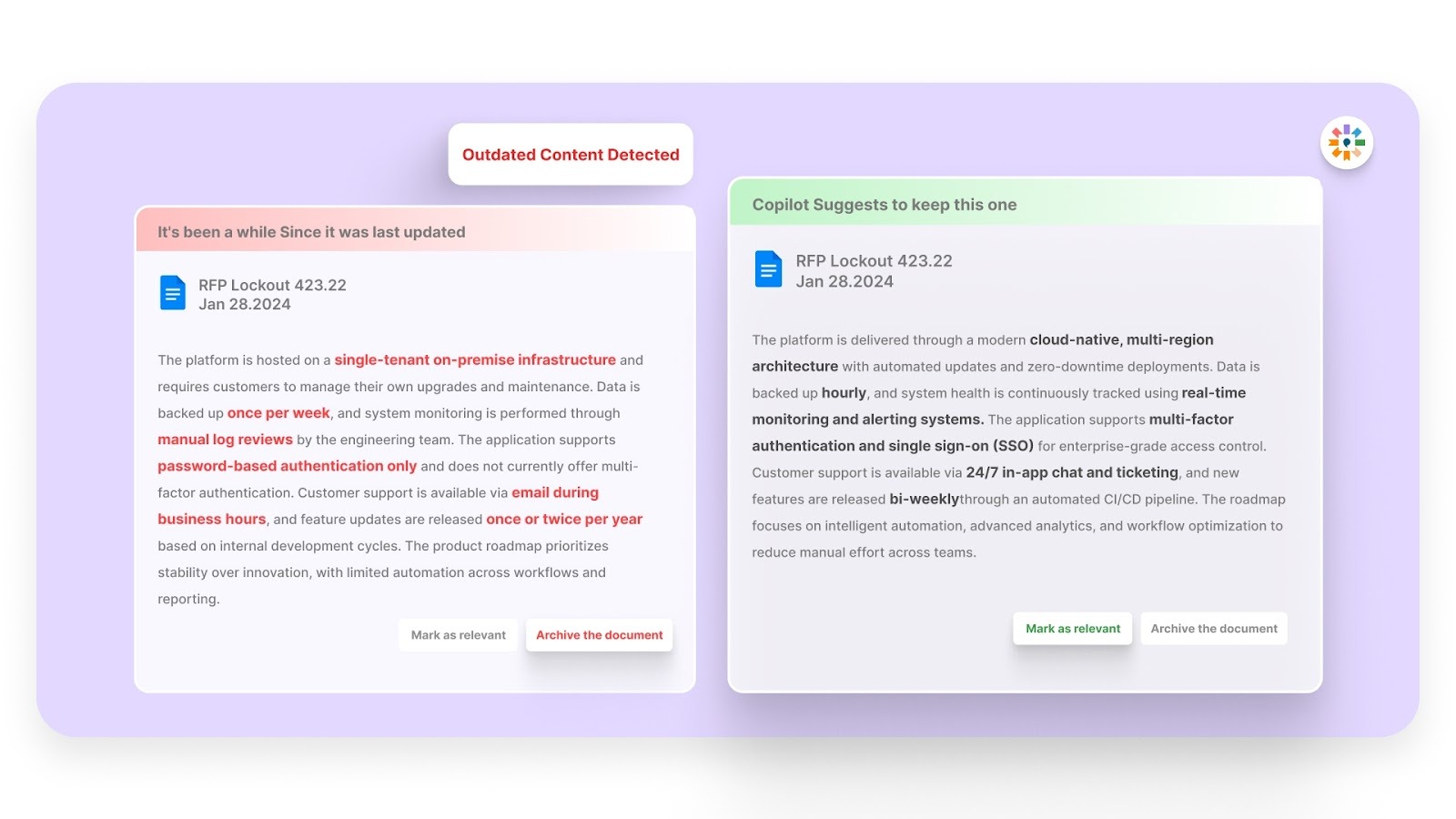
Security policies and tools change over time. Using outdated information can create compliance risks. Inventive AI identifies outdated content and alerts you so you can update your responses.
5. Simple, Easy-to-Use Interface
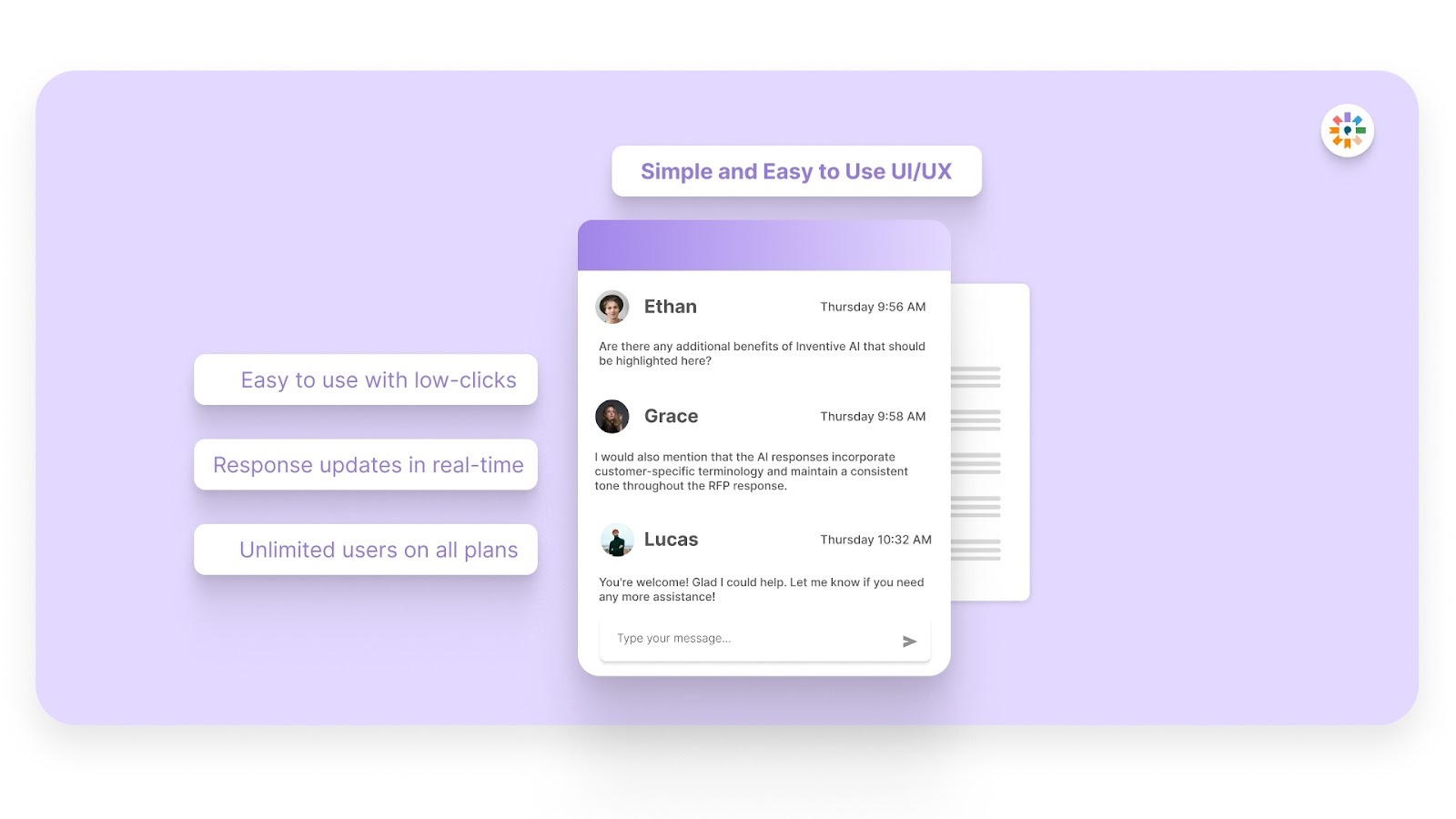
HIPAA questionnaires often require input from security, compliance, and product teams. Inventive AI provides a simple interface that helps teams quickly find information, generate answers, and manage questionnaire responses.
6. Narrative-Style Proposals
Inventive AI moves beyond simple Q&A by generating complete, long-form documents like executive summaries and one-pagers. Instead of just filling out spreadsheets, your team can deliver a persuasive, well-written story that clearly highlights your unique value to the buyer.
With Inventive AI, vendors can respond to HIPAA security assessments faster while keeping answers accurate and consistent.
Frequently Asked Questions (FAQs)
1. Does a Low Risk rating mean an organization is fully HIPAA compliant?
No, an SRA is only one part of compliance. You must also maintain ongoing administrative and physical safeguards, such as workforce training and incident response plans, to meet the full requirements of the HIPAA Security Rule.
2. Is there a difference between a HIPAA Risk Analysis and a Risk Assessment?
While often used interchangeably, the Risk Analysis is the formal process of identifying vulnerabilities, while the Risk Assessment is the broader program that includes documenting the analysis, implementing mitigation strategies, and continuous monitoring.
3. If we are SOC 2 Type II compliant, do we still need a separate HIPAA SRA?
Yes, SOC 2 focuses on general trust principles, whereas HIPAA is specifically mandated by law to address the protection of PHI. SOC 2 reports serve as excellent supporting documentation, but do not replace the legal requirement for a HIPAA-specific risk analysis.
4. How should we handle Risk Acceptance if mitigation is too expensive?
You must formally document the decision, provide a clear business justification, and implement alternative compensatory controls to ensure that any remaining risk stays at an acceptable level.
5. What does the term " addressable " mean regarding HIPAA encryption requirements?
Addressable does not mean optional; you must implement encryption if it is reasonable and appropriate, or document why it is not and use a secure, equivalent alternative measure instead

90% Faster RFPs. 50% More Wins. Watch a 2-Minute Demo.
After witnessing the gap between generic AI models and the high precision required for business proposals, Gaurav co-founded Inventive AI to bring true intelligence to the RFP process. An IIT Roorkee graduate with deep expertise in building Large Language Models (LLMs), he focuses on ensuring product teams spend less time on repetitive technical questionnaires and more time on innovation.
Understanding that sales leaders struggle to cut through the hype of generic AI, Mukund focuses on connecting enterprises with the specialized RFP automation they actually need at Inventive AI. An IIT Jodhpur graduate with 3+ years in growth marketing, he uses data-driven strategies to help teams discover the solution to their proposal headaches and scale their revenue operations.


.avif)