SOC RFP Template: Prepare Audit-Ready Vendor Security Proposals

Ensuring vendor cybersecurity compliance is a top procurement priority due to increased audit scrutiny on third-party services. As a result, many organizations now issue formal Security Operations Center (SOC) RFP templates to evaluate vendors’ security controls, compliance posture, and operational capabilities.
For vendors, these RFPs play a major role in determining eligibility for contracts, renewals, and long-term partnerships. Providing structured, evidence-backed responses helps demonstrate your security maturity and improves how buyers assess your SOC capabilities.
In this blog, you’ll learn how SOC RFP templates are used in vendor security evaluations and how a SOC RFP response template can help you prepare clear, accurate, and well-structured submissions.
SOC RFP Template: Key Criteria Buyers Use to Score Your Proposal

Enterprises use SOC RFP templates to assess vendor security across operational, technical, and compliance dimensions. These structured evaluations guide contract awards, risk mitigation, and audit readiness.
- Organization Overview & Project Overview: Provides background about the issuing organization and its cybersecurity priorities. It also explains the purpose of the RFP and the objectives for procuring SOC services.
- Scope of SOC Services: Defines the SOC capabilities and services the organization requires, such as monitoring, threat detection, and incident response. This section clarifies the functional scope vendors must support.
- Security & Compliance Requirements: Lists the regulatory standards and frameworks vendors must align with. It ensures the SOC provider can meet the organization’s compliance and security obligations.
- SOC Operational Requirements: Describes operational expectations, including monitoring coverage, incident response timelines, reporting frequency, and technology integration. It ensures SOC operations align with the buyer’s security environment.
- Vendor Qualification Requirements: Outlines the minimum experience, certifications, and capabilities vendors must possess. It helps buyers screen vendors before a detailed evaluation.
- Vendor Information & Experience: Collects vendor details, certifications, SOC technologies, and past project experience. This allows buyers to evaluate the credibility and expertise of providers delivering SOC services.
- Pricing Proposal: Request pricing details for SOC monitoring, incident response, compliance reporting, and additional services. Buyers use this section to compare vendor cost structures.
- Proposal Evaluation Criteria: Explains how vendor proposals will be assessed and the weight assigned to each category. It ensures transparency in the vendor selection process.
- Proposal Submission Instructions & Terms: Provides instructions on proposal format, submission method, and deadlines. It also outlines procurement conditions such as the buyer’s right to reject proposals.
- Vendor Evaluation Scorecard (Optional): Provides an internal scoring table to compare vendor proposals across technical, compliance, experience, and pricing factors. Procurement teams use it to record and analyze evaluation results.
While the buyer makes the final evaluation, the evidence you provide strongly influences how your security posture is assessed. Here’s how you can respond effectively.
SOC RFP Response Template: Streamline Security Submissions (for Vendor)

To succeed in SOC RFP evaluations, you must present your security capabilities in a clear and structured way. Providing measurable data, compliance evidence, and operational details helps buyers accurately assess your security posture and consider you for contracts, renewals, and future RFP opportunities.
- Company Overview: Use this section to introduce your company and summarize your SOC service capabilities. It helps buyers understand your background, scale, and experience in delivering security operations services.
- SOC Service Overview: Explain the SOC service model you provide and the types of monitoring and security services you offer. This allows buyers to see how your SOC structure aligns with their operational needs.
- Security & Compliance Capabilities: List the security frameworks and compliance standards your SOC services support. Providing this information helps buyers verify that your services meet their regulatory and security requirements.
- SOC Operational Capabilities: Describe how your SOC detects, manages, and responds to security incidents. This section helps buyers evaluate your operational processes, response times, and security technologies.
- Staffing & Expertise: Provide details about your SOC analysts, certifications, and training programs. Buyers use this information to assess the team's expertise and qualifications in managing their security environment.
- Client Experience: Share examples of past SOC engagements and relevant client references. This demonstrates your experience in delivering similar services and builds credibility with the buyer.
- Technology & Security Infrastructure: Describe the security platforms, monitoring tools, and infrastructure used by your SOC. Buyers use this information to understand how your technology stack supports threat detection and incident management.
- Pricing Proposal: Provide a clear breakdown of your pricing structure for SOC services. This helps buyers compare costs and understand the financial scope of your proposal.
- Supporting Documentation: Attach certifications, compliance reports, and sample SOC deliverables that validate your claims. These documents provide evidence of your security capabilities and operational practices.
- Response Summary: Summarize how your SOC services meet the buyer’s requirements outlined in the RFP. Use this section to reinforce your strengths and highlight why your solution is suitable for the engagement.
Also Read: Guide To RFP Response Process
Even with a well-structured SOC RFP response template, certain mistakes can weaken your submission and affect how buyers evaluate your proposal. Let’s explore some common issues and how you can avoid them.
How Vendors Can Avoid Losing Points in SOC RFPs?
When you respond to a SOC RFP, buyers expect clear evidence of your security controls, compliance posture, and operational maturity. Submissions that lack documentation, contain inconsistent metrics, or present unstructured explanations can reduce your evaluation score.
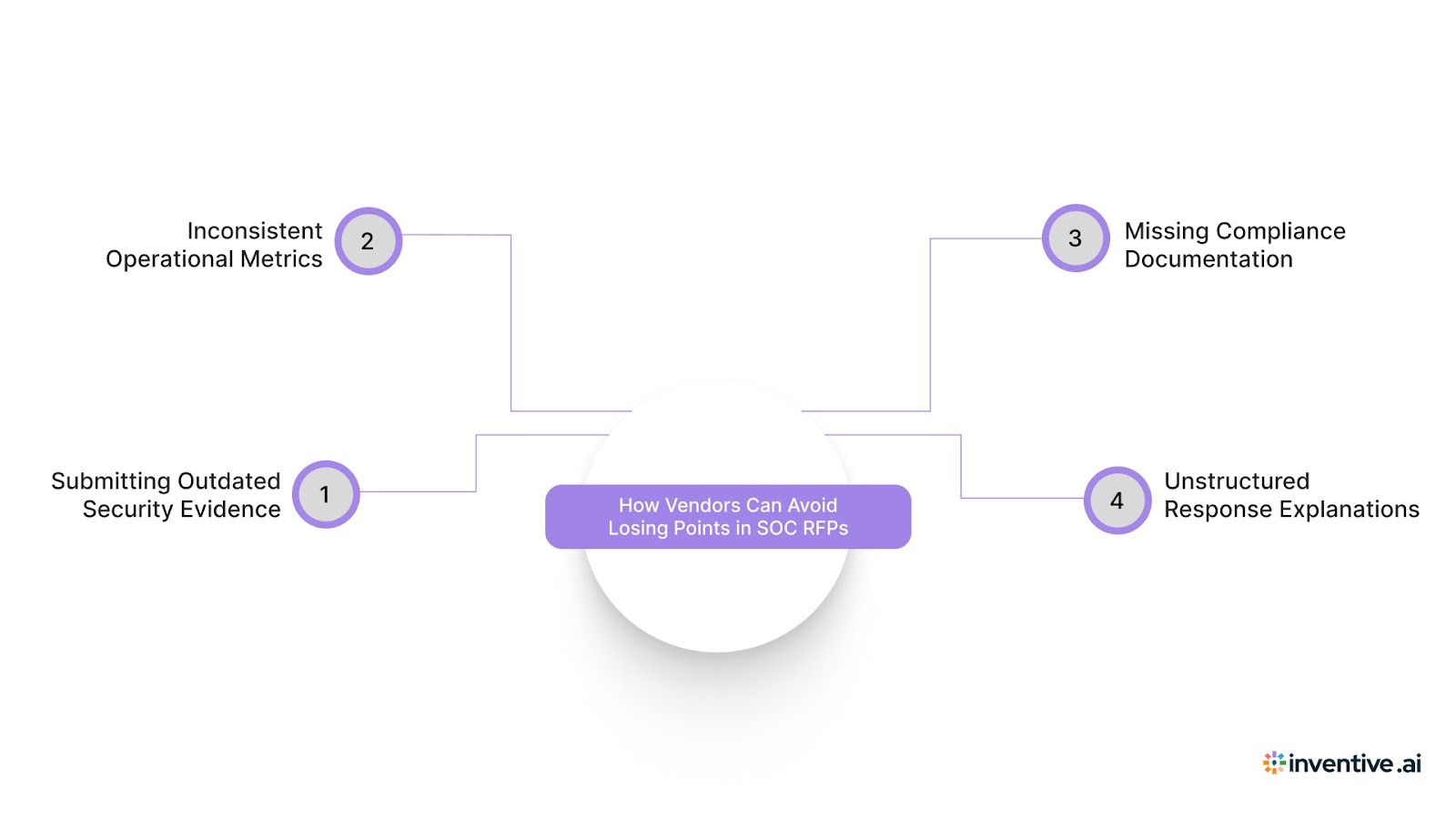
Here are some common issues and how you can address them:
1. Submitting Outdated Security Evidence
Providing expired SOC reports, outdated certifications, or old penetration test results can raise concerns about the current state of your security controls.
Fix: Include your most recent SOC 2 Type II report, ISO certifications, vulnerability assessments, and penetration test summaries. Ensure all documents reflect the latest audit period and implemented security controls.
2. Inconsistent Metrics Across Sections
Metrics such as incident response times, monitoring coverage, or analyst staffing levels sometimes differ across sections of your response. These inconsistencies can create doubts about the accuracy of your operational data.
Fix: Align all operational metrics with a single internal source, such as your SOC performance dashboard or SLA documentation. Verify that response times, coverage hours, and staffing numbers remain consistent throughout the submission.
3. Missing Compliance Documentation
Stating compliance with frameworks such as SOC 2 or ISO 27001 without providing supporting documentation makes it difficult for buyers to validate your claims.
Fix: Attach relevant audit reports, certification letters, security policies, and compliance attestations. Reference the applicable audit period and control framework to make verification easier.
4. Unstructured or Overly Long Explanations
Lengthy narrative responses without measurable data can make it harder for evaluators to identify your SOC capabilities.
Fix: Structure responses using concise explanations supported by measurable metrics such as mean time to detect (MTTD), mean time to respond (MTTR), monitoring coverage hours, and escalation timelines.
Also Read: RFP Response Trends and Benchmarks: Key Insights for 2026
As RFP volumes grow, maintaining consistency and accuracy manually becomes difficult. This is where intelligent automation plays a critical role.
How Inventive AI Simplifies SOC RFP Responses?
Responding to SOC RFPs manually can be time-consuming, especially when security documentation, compliance evidence, and past responses are stored across multiple teams and systems.
Inventive AI centralizes this information in a unified knowledge hub and uses AI-powered drafting to generate structured responses based on previous RFPs and security questionnaires.
Key Capabilities of Inventive AI:
2x Higher Response Quality
Multi-agent AI generates structured, complete responses that typically require minimal revision, improving submission consistency and enabling RFPs to be completed up to 90% faster.
Context-Awareness
Inventive AI evaluates the entire RFP, including scope, compliance requirements, and evaluation criteria. Responses align with project-specific requirements rather than relying on static boilerplate, helping vendors achieve up to 50% higher win rates.
Instant Conflict Detection Before Submission
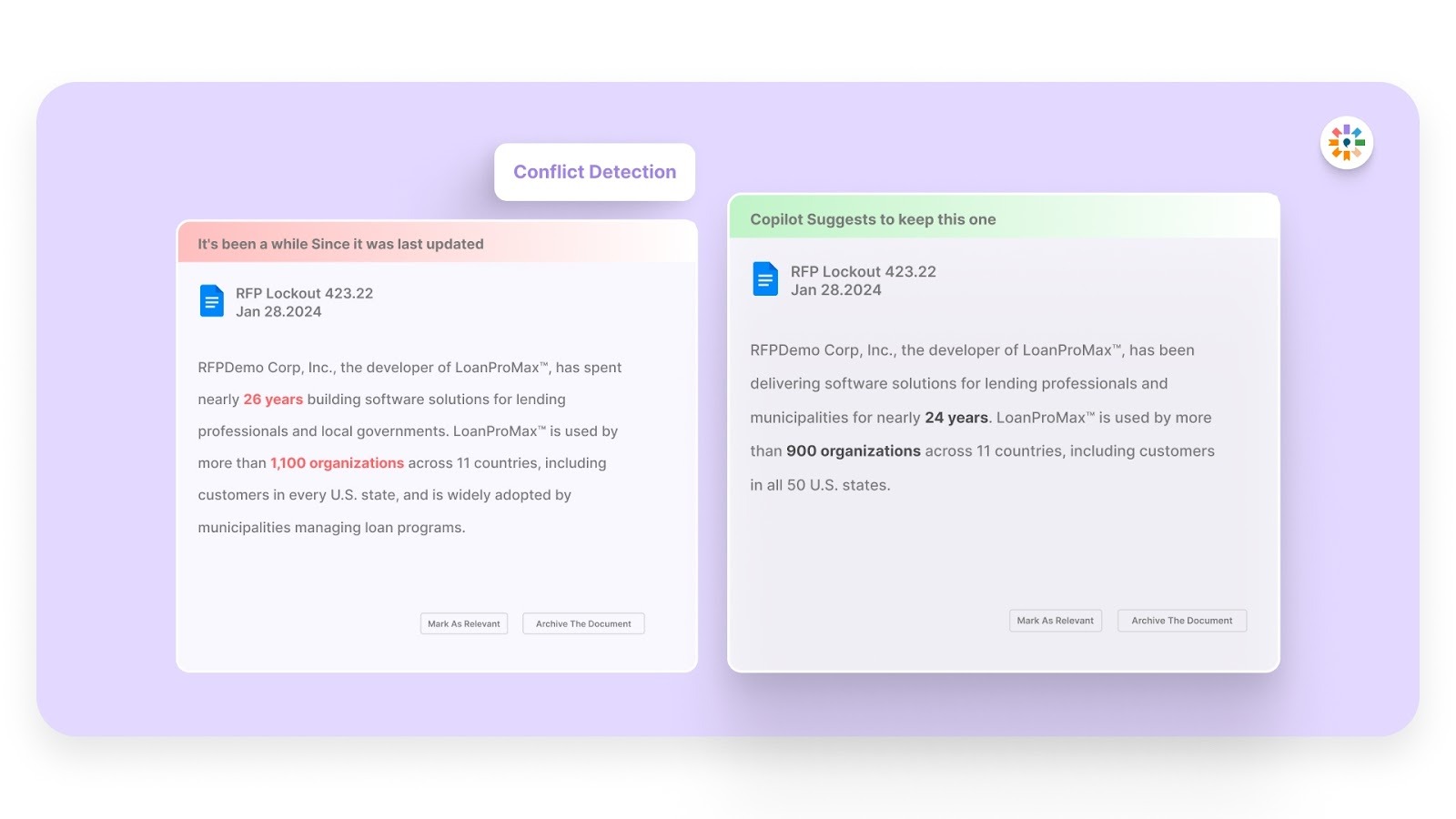
Avoid costly mistakes by having Inventive AI identify and resolve any inconsistencies or conflicts in your responses before submission, ensuring that everything is aligned and accurate.
Outdated Content Detection
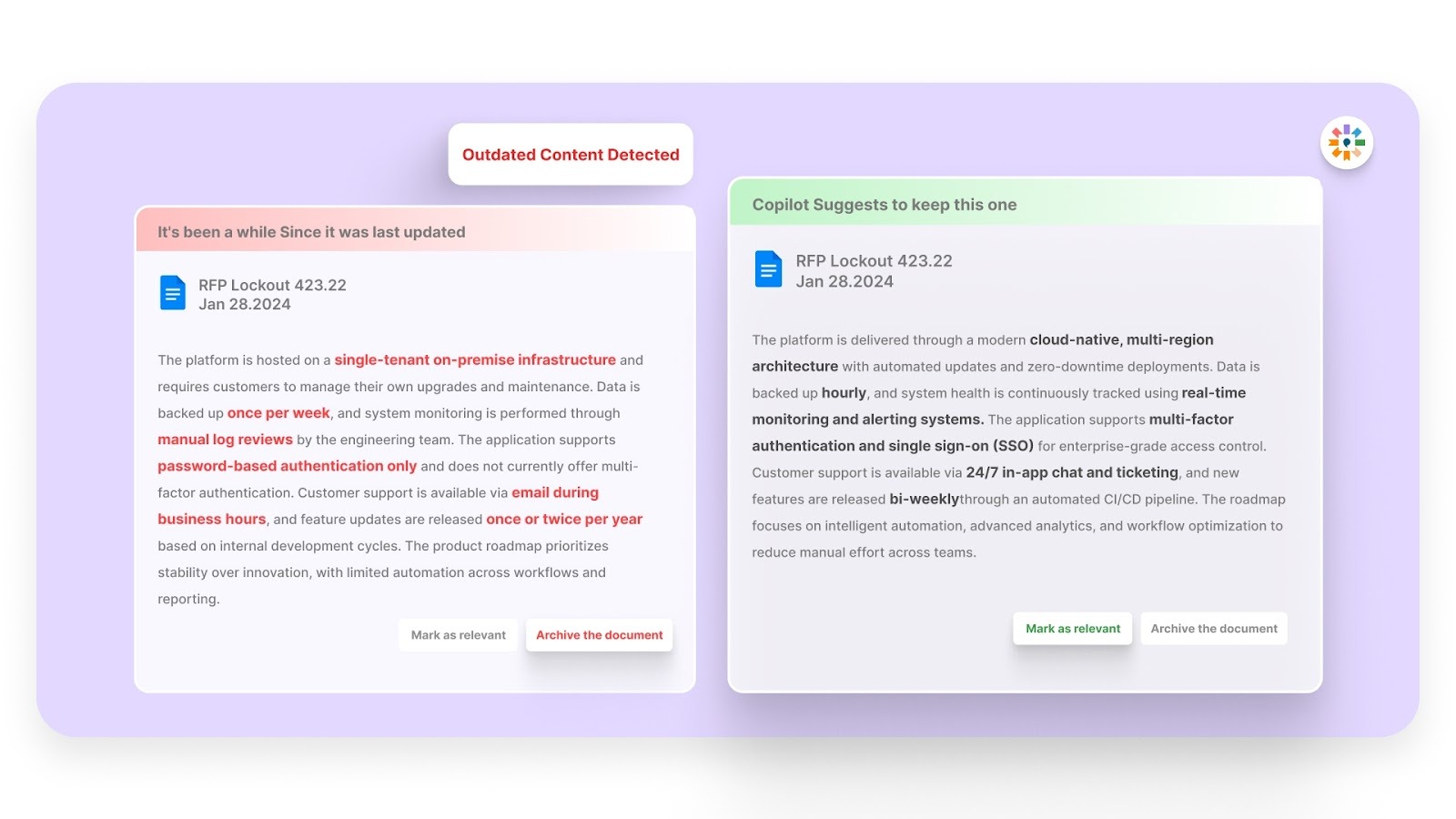
Never submit outdated information again. Inventive AI automatically flags and updates any content that is no longer relevant, so your responses stay fresh and aligned with the latest industry standards.
Narrative-Style Proposals
Say goodbye to fragmented, disjointed answers. Inventive AI ensures your proposals are cohesive, professional, and tell a compelling story that resonates with the buyer.
Simple, Easy-to-Use Interface
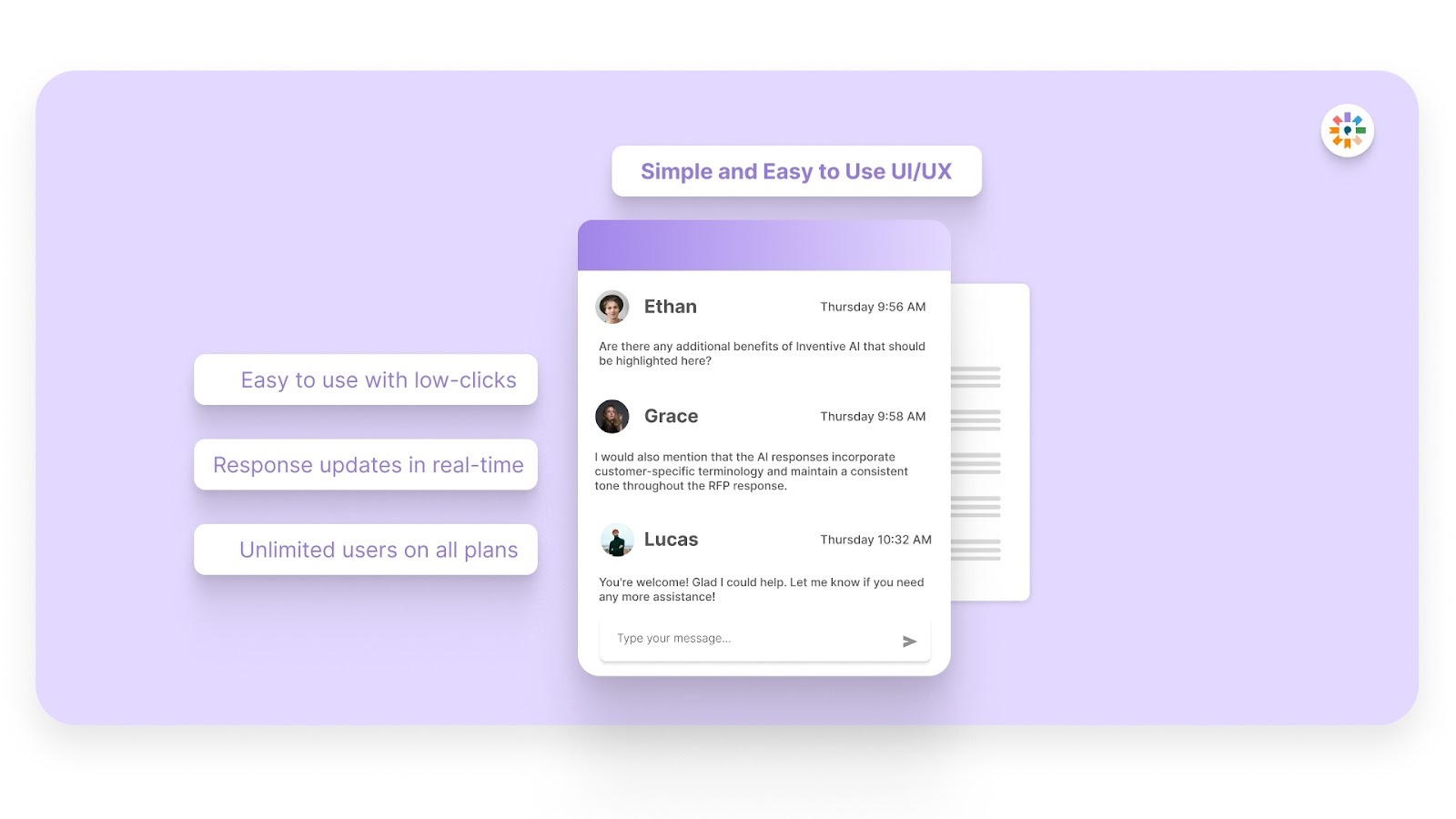
Inventive AI lets all stakeholders, including HR, sales, legal, and compliance, contribute directly, reducing coordination delays and keeping RFP responses on track.
FAQs
1. How long does it typically take vendors to prepare a SOC RFP response?
Preparation time varies depending on the complexity of the SOC requirements and the availability of documentation. Vendors with organized security documentation and pre-approved responses can often complete submissions faster than those who must assemble information from multiple teams.
2. Should vendors customize responses for each SOC RFP or reuse standard answers?
Vendors should reuse validated security information where appropriate, but customize responses to match the buyer’s environment, compliance requirements, and monitoring scope. Tailored responses demonstrate that the vendor understands the organization’s security priorities and operational needs.
3. Who should be involved internally when preparing a SOC RFP response?
SOC RFP responses typically require collaboration between security operations teams, compliance specialists, proposal managers, and legal stakeholders. Each group contributes technical details, certifications, operational metrics, and contractual information required for a complete submission.
4. What types of supporting documents strengthen a SOC RFP response?
Supporting materials such as SOC audit reports, security policies, incident response playbooks, architecture diagrams, and sample monitoring reports can strengthen a submission. These documents provide verifiable evidence of operational practices and security governance.
5. How can vendors ensure their SOC RFP responses remain consistent across multiple submissions?
Maintaining a centralized repository of approved security responses and documentation helps vendors maintain consistency. Regularly reviewing and updating this content ensures that future SOC RFP submissions reflect current security controls, compliance status, and operational capabilities.

90% Faster RFPs. 50% More Wins. Watch a 2-Minute Demo.
After witnessing the gap between generic AI models and the high precision required for business proposals, Gaurav co-founded Inventive AI to bring true intelligence to the RFP process. An IIT Roorkee graduate with deep expertise in building Large Language Models (LLMs), he focuses on ensuring product teams spend less time on repetitive technical questionnaires and more time on innovation.
Understanding that sales leaders struggle to cut through the hype of generic AI, Mukund focuses on connecting enterprises with the specialized RFP automation they actually need at Inventive AI. An IIT Jodhpur graduate with 3+ years in growth marketing, he uses data-driven strategies to help teams discover the solution to their proposal headaches and scale their revenue operations.


.avif)